- Essentials
- Getting Started
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Monitor Template
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- OpenTelemetry
- Administrator's Guide
- API
- Datadog Mobile App
- CoScreen
- CoTerm
- Cloudcraft (Standalone)
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Monitors and Alerting
- Metrics
- Watchdog
- Bits AI
- Software Catalog
- Error Tracking
- Change Tracking
- Service Management
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- Hosts
- Containers
- Processes
- Serverless
- Network Monitoring
- Cloud Cost
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Setting Up Postgres
- Setting Up MySQL
- Setting Up SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Connecting DBM and Traces
- Data Collected
- Exploring Database Hosts
- Exploring Query Metrics
- Exploring Query Samples
- Exploring Recommendations
- Troubleshooting
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Real User Monitoring
- Synthetic Testing and Monitoring
- Continuous Testing
- Product Analytics
- Software Delivery
- CI Visibility
- CD Visibility
- Test Optimization
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Code Security
- Cloud Security
- App and API Protection
- Workload Protection
- Sensitive Data Scanner
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
Connect an Amazon EKS Cluster with Cloudcraft
By scanning your Amazon EKS clusters, Cloudcraft allows you to generate system architecture diagrams to help visualize your deployed workloads and pods.
Cloudcraft uses access entries to grant Cloudcraft’s existing read-only IAM entity role access to the Kubernetes API. Cloudcraft does not require any special software or agent to be installed on your cluster.
The ability to scan Amazon EKS clusters and AWS accounts is only available to Cloudcraft Pro subscribers. Check out our pricing page for more information.
Prerequisites
Before connecting your Amazon EKS clusters with Cloudcraft, you must connect your AWS account and generate diagrams that include your clusters.
To connect your AWS account and familiarize yourself with Cloudcraft, see the following articles:
- Connect your AWS account with Cloudcraft
- Crafting Better Diagrams: Cloudcraft’s Live Diagramming and Filtering
Install and configure kubectl, a tool that allows you to control Kubernetes clusters through the command line. Cloudcraft recommends using the latest version to avoid issues.
In addition, you’ll want to install and configure the AWS CLI to manage your AWS services from the command line. As with kubectl, Cloudcraft recommends using the latest version.
Finally, in order to scan your cluster successfully, Cloudcraft requires clusters to have public access enabled and no IP filtering applied. The Public Access Source Allow List option in the networking configuration must remain set to its default value of 0.0.0.0/0.
Create access entries
Start by opening a blueprint with an existing Amazon EKS cluster or creating a new blueprint to scan an account with Amazon EKS clusters.
With your AWS environment mapped into a blueprint, select the Amazon EKS cluster that you wish to scan, and click the Enable cluster scanning button that appears in the component toolbar.
The next screen provides step-by-step commands to run in your favorite terminal application.
As the Amazon EKS cluster creator or user with admin access, run the following command to map the Cloudcraft IAM role to the Kubernetes group cloudcraft-view-only:
aws eks create-access-entry \
--cluster-name ${EKS_CLUSTER_NAME} \
--principal-arn ${CLOUDCRAFT_IAM_ROLE_ARN} \
--kubernetes-groups 'cloudcraft-view-only'
Granting view-only access to the Cloudcraft IAM role
Next, use ClusterRoleBinding to bind the IAM role to a Kubernetes role.
A ClusterRoleBinding grants permissions defined in a role to a user or set of users in all namespaces in a cluster. Kubernetes defines some default user-facing roles. For Cloudcraft, use the predefined “view” role that allows view-only access to most objects in a namespace.
Enter the following multi-line command to create the ClusterRoleBinding and grant view-only permission to users in the cloudcraft-view-only group.
cat << EOF | kubectl apply -f -
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: cloudcraft-view-only
subjects:
- kind: Group
name: cloudcraft-view-only
apiGroup: rbac.authorization.k8s.io
roleRef:
kind: ClusterRole
name: view
apiGroup: rbac.authorization.k8s.io
EOF
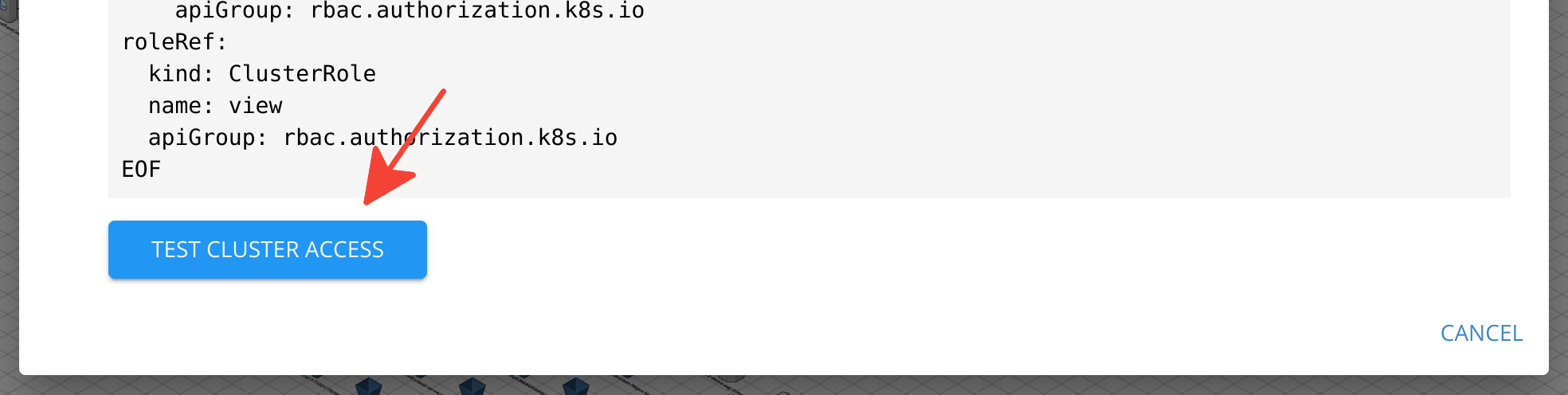
Testing access to the cluster
To test that Cloudcraft can access to the cluster, click Test cluster access at the bottom of the Enable Kubernetes Cluster Scanning screen.
To scan other clusters, repeat the process as many times as needed.