- Essentials
- Getting Started
- Datadog
- Datadog Site
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Integrations
- Containers
- Dashboards
- Monitors
- Logs
- APM Tracing
- Profiler
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic Monitoring
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- OpenTelemetry
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- API
- Datadog Mobile App
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- Monitors and Alerting
- Infrastructure
- Metrics
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Real User Monitoring
- Product Analytics
- Synthetic Testing and Monitoring
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
Code Security
Overview
Datadog Code Security identifies code-level vulnerabilities in your services and provides actionable insights and recommended fixes.
For a list of supported services, see the Library Compatibility Requirements.
Code Security uses an Interactive Application Security Testing (IAST) approach to find vulnerabilities within your application code. IAST uses instrumentation embedded in your code like application performance monitoring (APM).
Code Security also monitors your code’s interactions with other components of your stack, such as libraries and infrastructure.
IAST enables Datadog to identify vulnerabilities using legitimate application traffic instead of relying on external tests that could require extra configuration or periodic scheduling.
Code Security’s runtime application monitoring provides an up-to-date view of your attack surface that enables you to quickly identify potential issues.
Code-level vulnerabilities list
The Code Security detection rules support the following languages.
| Severity | Detection Rule | Java | .NET | Node.js | Python |
|---|---|---|---|---|---|
| Critical | NoSQL Injection | FALSE | TRUE | TRUE | FALSE |
| Critical | SQL Injection | TRUE | TRUE | TRUE | TRUE |
| Critical | Server-Side Request Forgery (SSRF) | TRUE | TRUE | TRUE | TRUE |
| Critical | Command Injection | TRUE | TRUE | TRUE | TRUE |
| High | LDAP Injection | TRUE | TRUE | TRUE | FALSE |
| High | Hardcoded Secrets | TRUE | TRUE | TRUE | FALSE |
| High | Hardcoded Passwords | FALSE | FALSE | TRUE | FALSE |
| High | Path Traversal | TRUE | TRUE | TRUE | TRUE |
| High | Trust Boundary Violation | TRUE | TRUE | FALSE | FALSE |
| High | Cross-Site Scripting (XSS) | TRUE | TRUE | FALSE | FALSE |
| High | Unvalidated Redirect | TRUE | TRUE | TRUE | FALSE |
| High | XPath Injection | TRUE | TRUE | FALSE | FALSE |
| High | Header Injection | TRUE | TRUE | TRUE | TRUE |
| High | Directory Listing Leak | TRUE | FALSE | FALSE | FALSE |
| High | Default HTML Escape Invalid | TRUE | FALSE | FALSE | FALSE |
| High | Verb Tampering | TRUE | FALSE | FALSE | FALSE |
| Medium | No SameSite Cookie | TRUE | TRUE | TRUE | TRUE |
| Medium | Insecure Cookie | TRUE | TRUE | TRUE | TRUE |
| Medium | No HttpOnly Cookie | TRUE | TRUE | TRUE | TRUE |
| Medium | Weak Hashing | TRUE | TRUE | TRUE | TRUE |
| Medium | Weak Cipher | TRUE | TRUE | TRUE | TRUE |
| Medium | Stacktrace Leak | TRUE | TRUE | FALSE | FALSE |
| Medium | Reflection Injection | TRUE | TRUE | FALSE | FALSE |
| Medium | Insecure Authentication Protocol | TRUE | TRUE | FALSE | FALSE |
| Medium | Hardcoded Key | FALSE | TRUE | FALSE | FALSE |
| Medium | Insecure JSP Layout | TRUE | FALSE | FALSE | FALSE |
| Low | HSTS Header Missing | TRUE | TRUE | TRUE | FALSE |
| Low | X-Content-Type-Options Header Missing | TRUE | TRUE | TRUE | FALSE |
| Low | Weak Randomness | TRUE | TRUE | TRUE | TRUE |
| Low | Admin Console Active | TRUE | FALSE | FALSE | FALSE |
| Low | Session Timeout | TRUE | FALSE | FALSE | FALSE |
| Low | Session Rewriting | TRUE | FALSE | FALSE | FALSE |
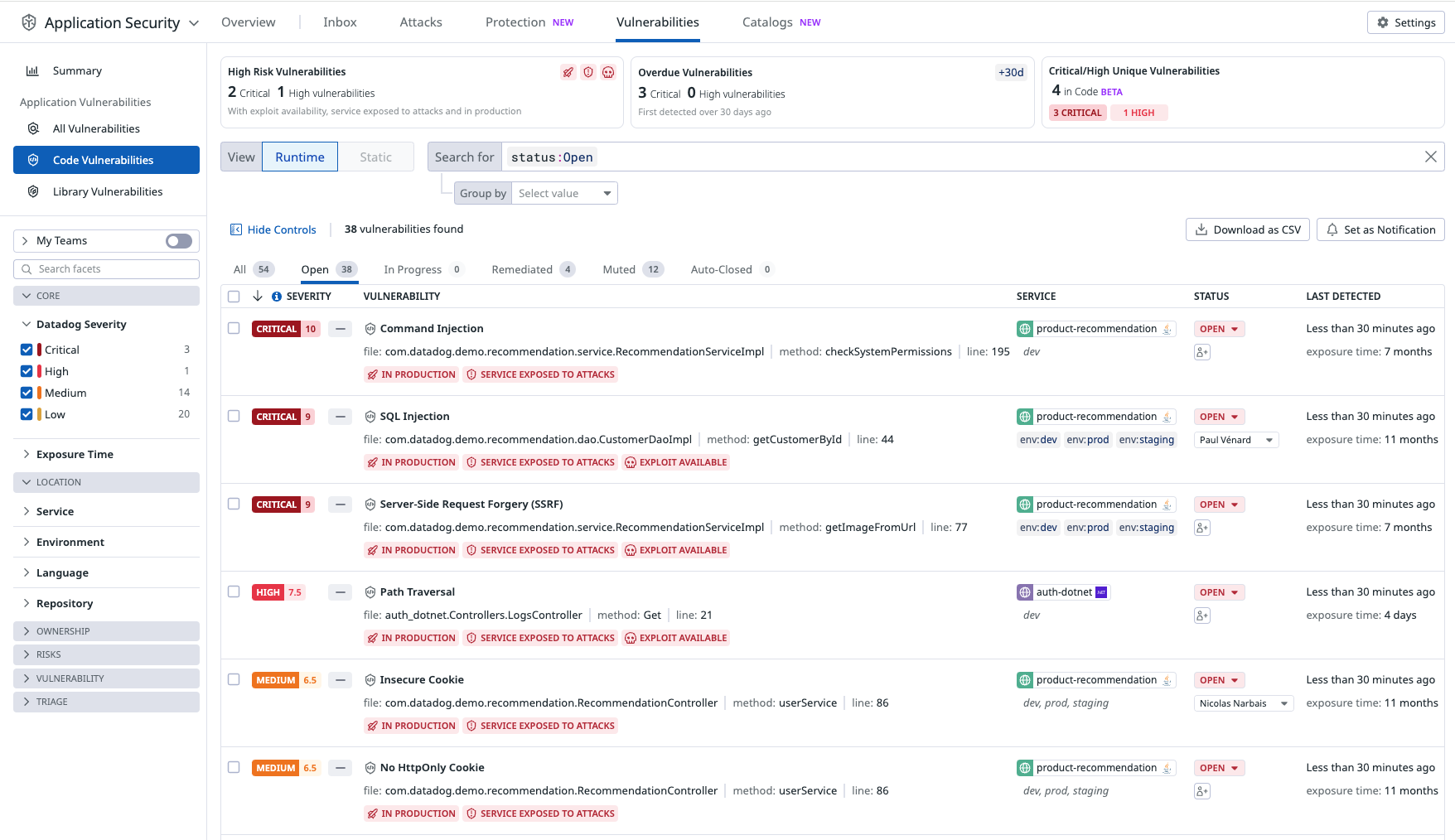
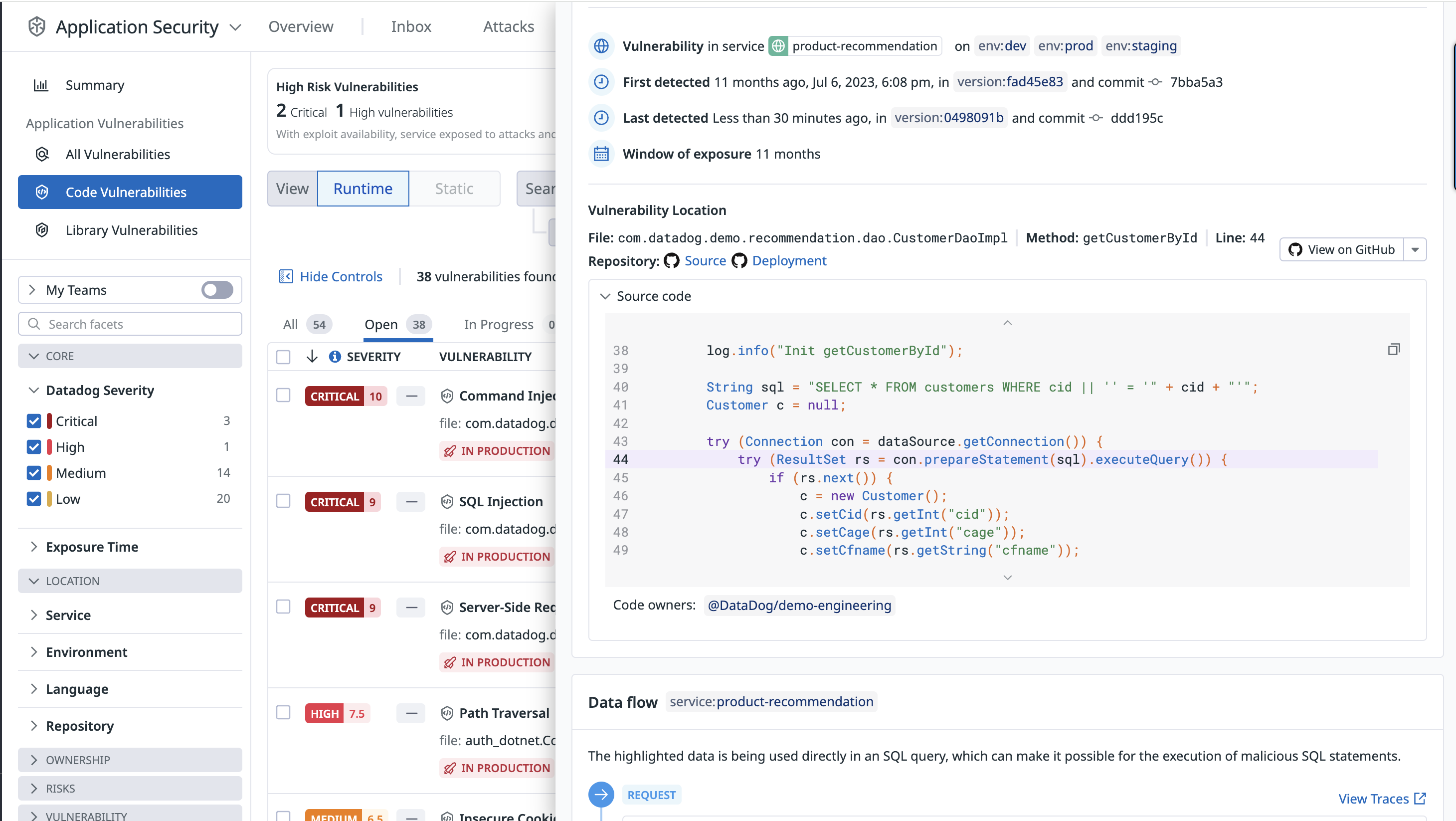
Explore and manage code vulnerabilities
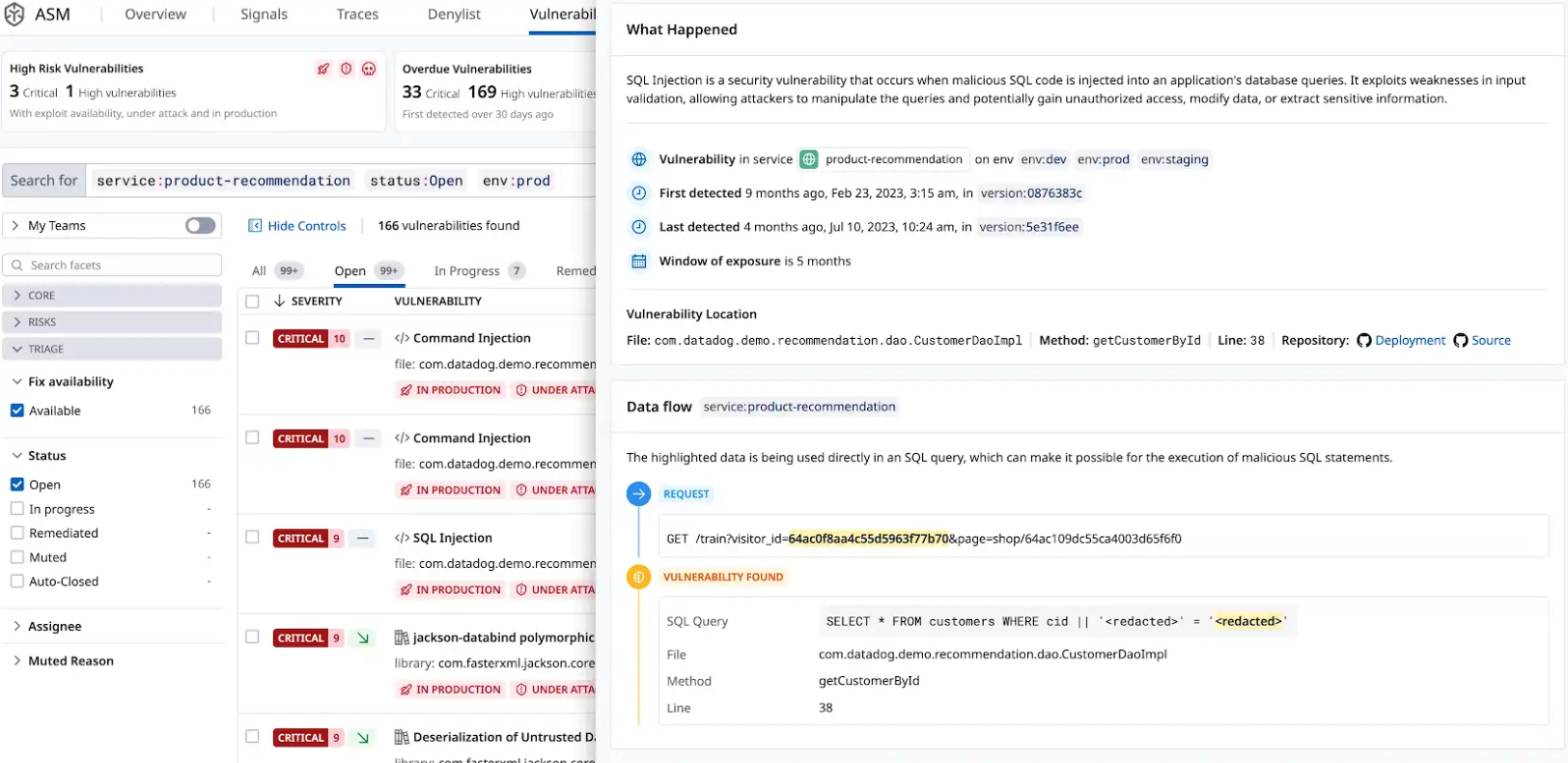
The Vulnerability Explorer uses real-time threat data to help you understand vulnerabilities endangering your system. Vulnerabilities are ordered by severity.
To triage vulnerabilities, each vulnerability contains a brief description of the issue, including:
- Impacted services.
- Vulnerability type.
- First detection.
- The exact file and line number where the vulnerability was found.
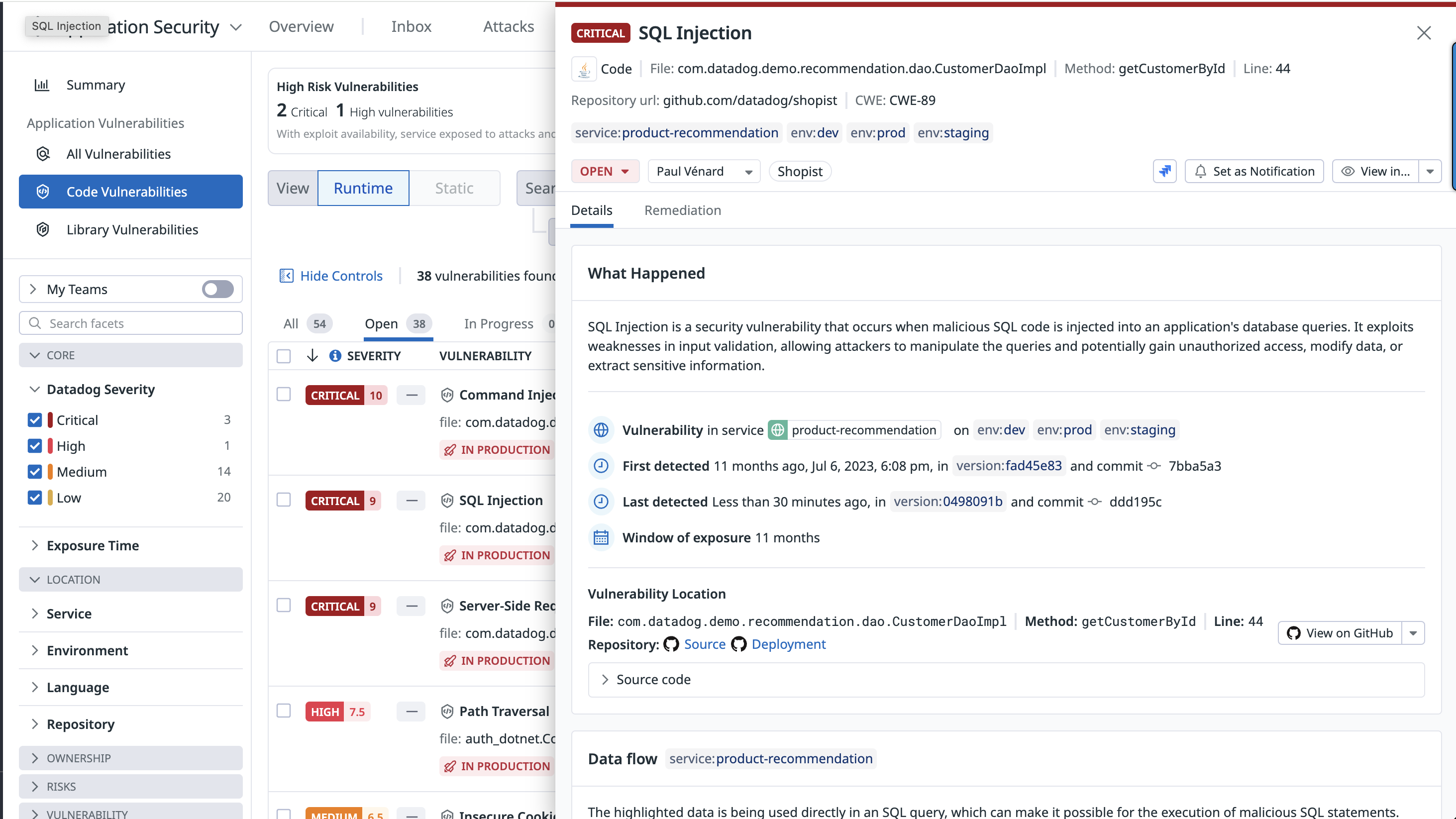
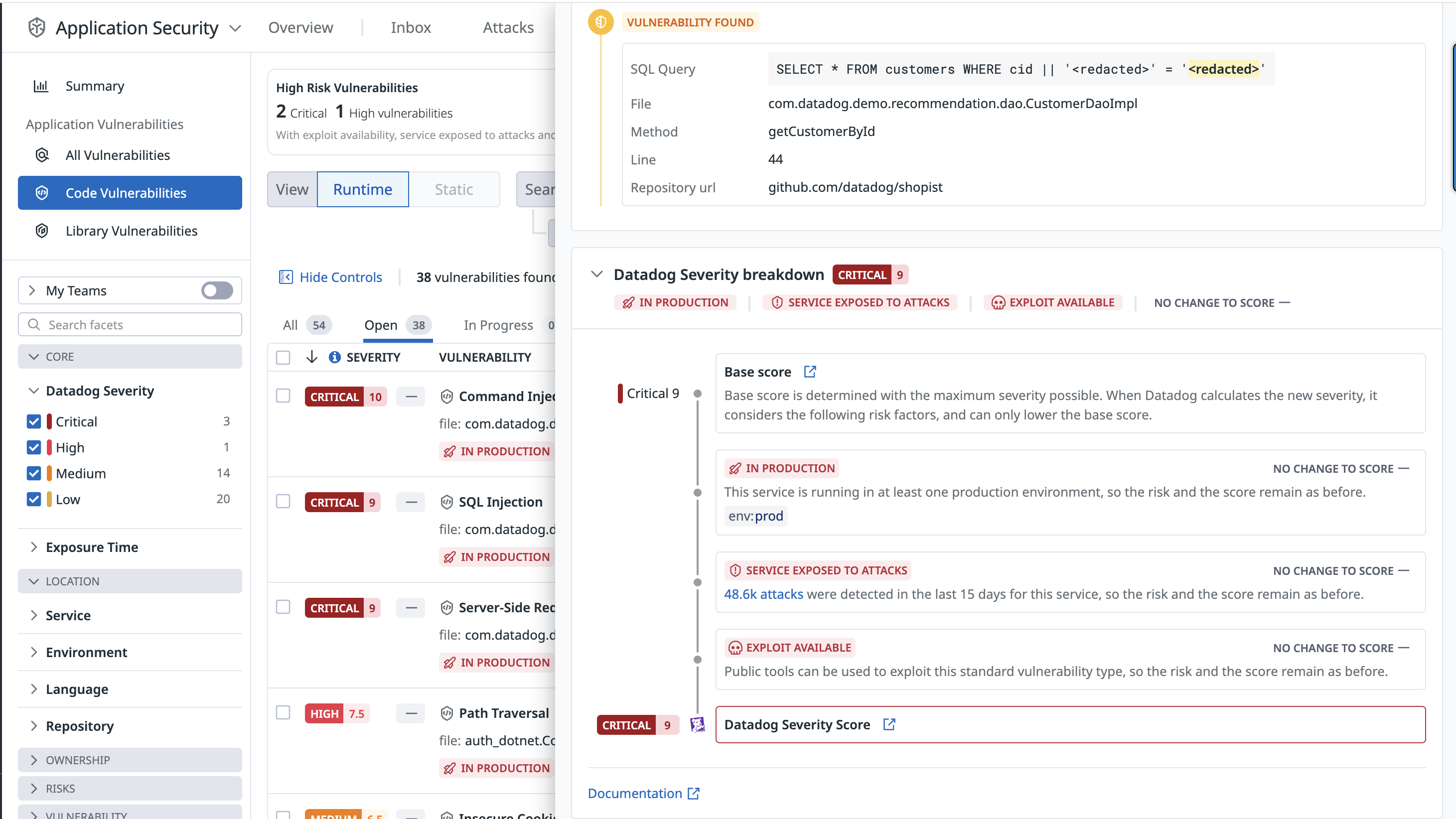
Each vulnerability detail includes a risk score (see screenshot below) and a severity rating: critical, high, medium, or low.
The risk score is tailored to the specific runtime context, including factors such as where the vulnerability is deployed and whether the service is targeted by active attacks.
Remediation
Datadog Code Security automatically provides the information teams need to identify where a vulnerability is in an application, from the affected filename down to the exact method and line number.
When the GitHub integration is enabled, Code Security shows the first impacted version of a service, the commit that introduced the vulnerability, and a snippet of the vulnerable code. This information gives teams insight into where and when a vulnerability occurred and helps to prioritize their work.
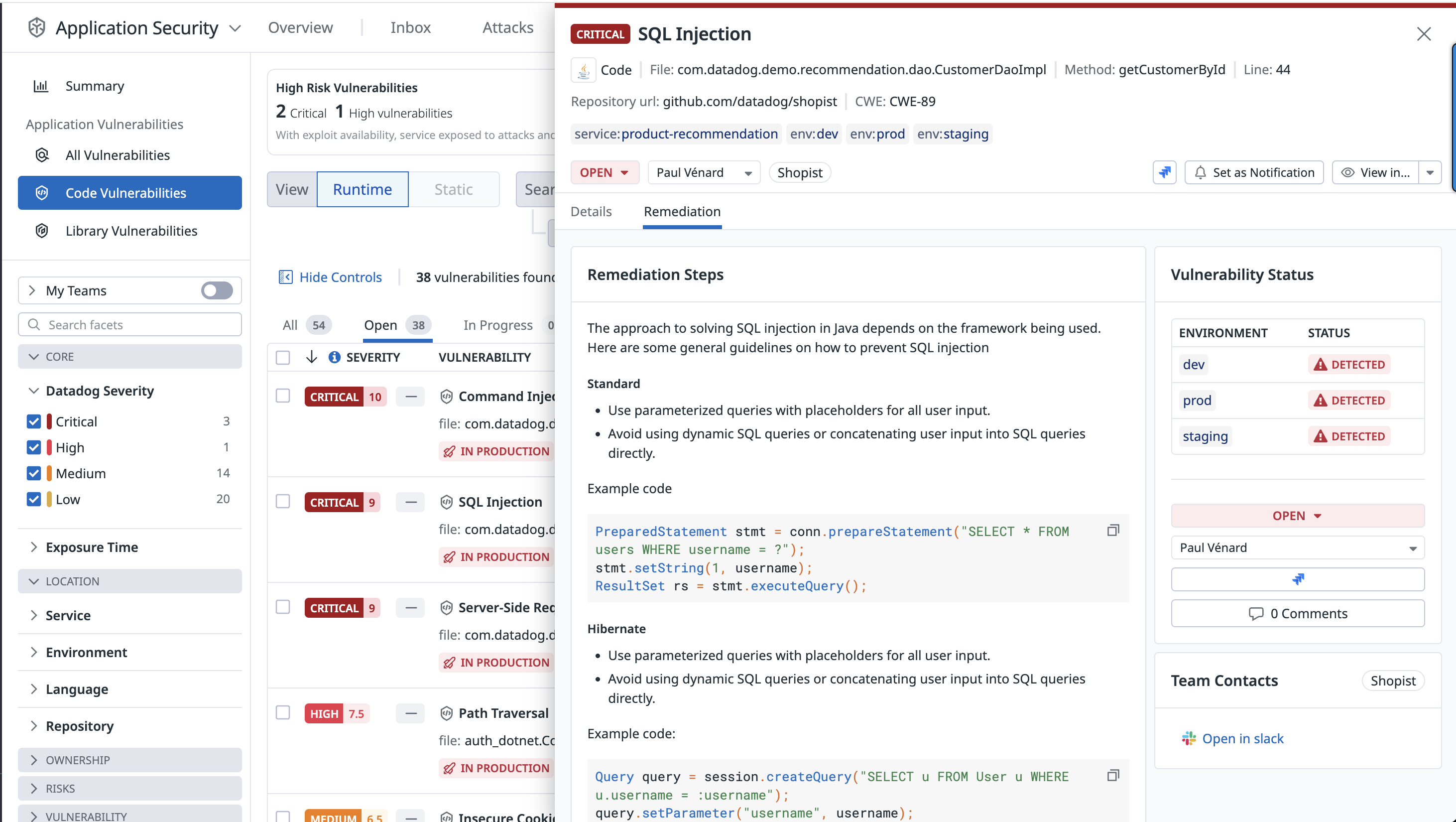
Detailed remediation steps are provided for each detected vulnerability.
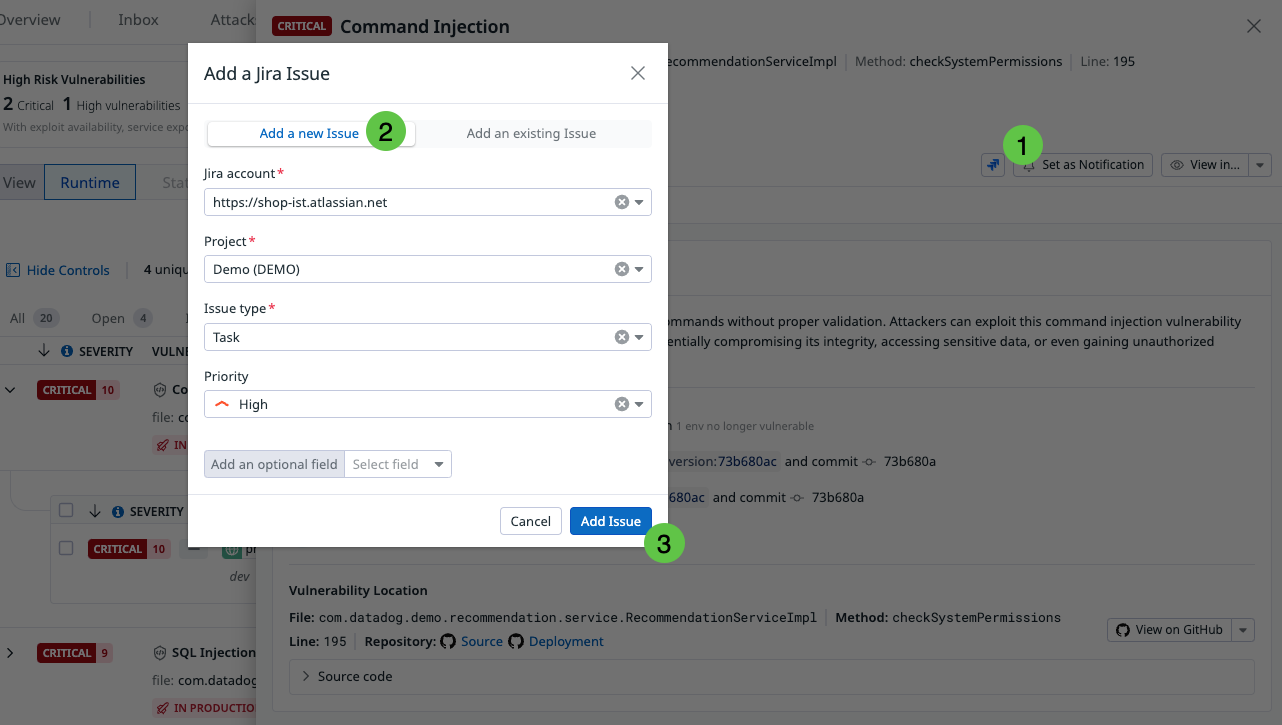
Recommendations enable you to change the status of a vulnerability, assign it to a team member for review, and create a Jira issue for tracking.
Note: To create Jira issues for vulnerabilities, you must configure the Jira integration, and have the manage_integrations permission. For detailed instructions, see the Jira integration documentation, as well as the Role Based Access Control documentation.
Enabling Code Security
To enable Code Security, you can use Single Step Instrumentation or configure the Datadog Tracing Library. Detailed instructions for both methods can be found in the Security > Application Security > Settings section.
If you need additional help, contact Datadog support.
Further Reading
Additional helpful documentation, links, and articles: