- Essentials
- Getting Started
- Datadog
- Datadog Site
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Integrations
- Containers
- Dashboards
- Monitors
- Logs
- APM Tracing
- Profiler
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic Monitoring
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Test Impact Analysis
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- OpenTelemetry
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- Administrator's Guide
- API
- Datadog Mobile App
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Sheets
- Monitors and Alerting
- Infrastructure
- Metrics
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Real User Monitoring
- Product Analytics
- Synthetic Testing and Monitoring
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Optimization
- Code Analysis
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
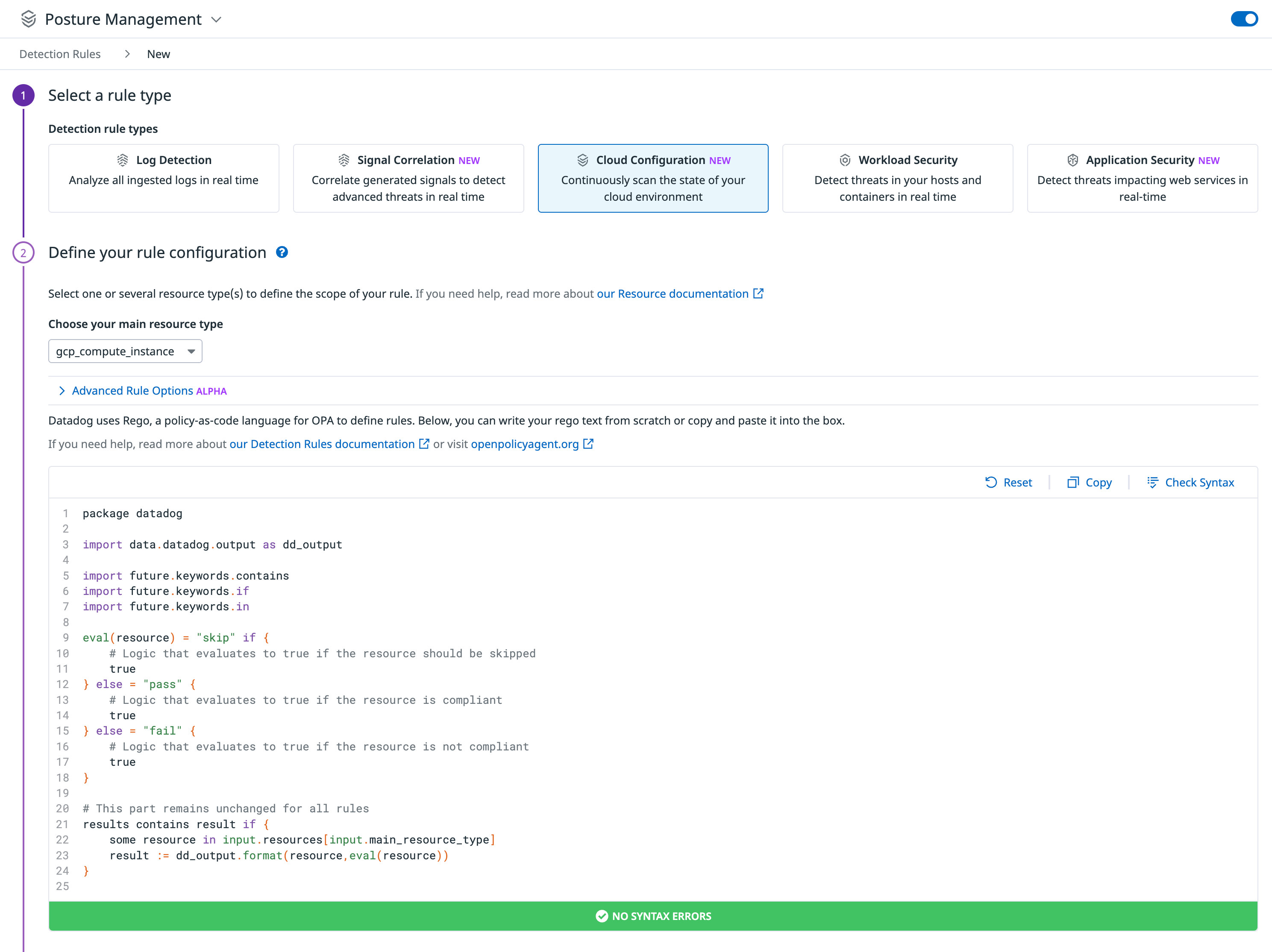
Create Custom Rules
Overview
To extend the rules being applied to your environment to evaluate your security posture, you can clone compliance rules and edit the copies, and you can create your own rules from scratch. To view the list of the available resource types for your custom rules, see Cloud Resources Schema.
Cloning rules
To clone a rule:
- Find the rule you want to copy by doing one of the following:
- Navigate to the Misconfigurations Rules page. Select a rule you want to copy to open its details page.
- Navigate to the Misconfigurations Explorer. Select a misconfiguration to open its details, then select Edit Rule.
- Make any changes you want for your new rule.
- Scroll to the bottom of the details page and click Clone Rule.
Creating rules
To create a rule from scratch:
Navigate to the Misconfigurations Rules page.
Click New Rule in the upper-right.
Select Cloud Configuration as the rule type.
Specify the cloud resource types you are writing the rule for.
Write the rule logic using Rego, a policy-as-code language, either from scratch or by using the Datadog template. Read Writing Custom Rules with Rego for more information. Note that you can mark a resource as “pass”, “fail”, or “skip”. If you do not mark a resource, it will be interpreted as “skip”.
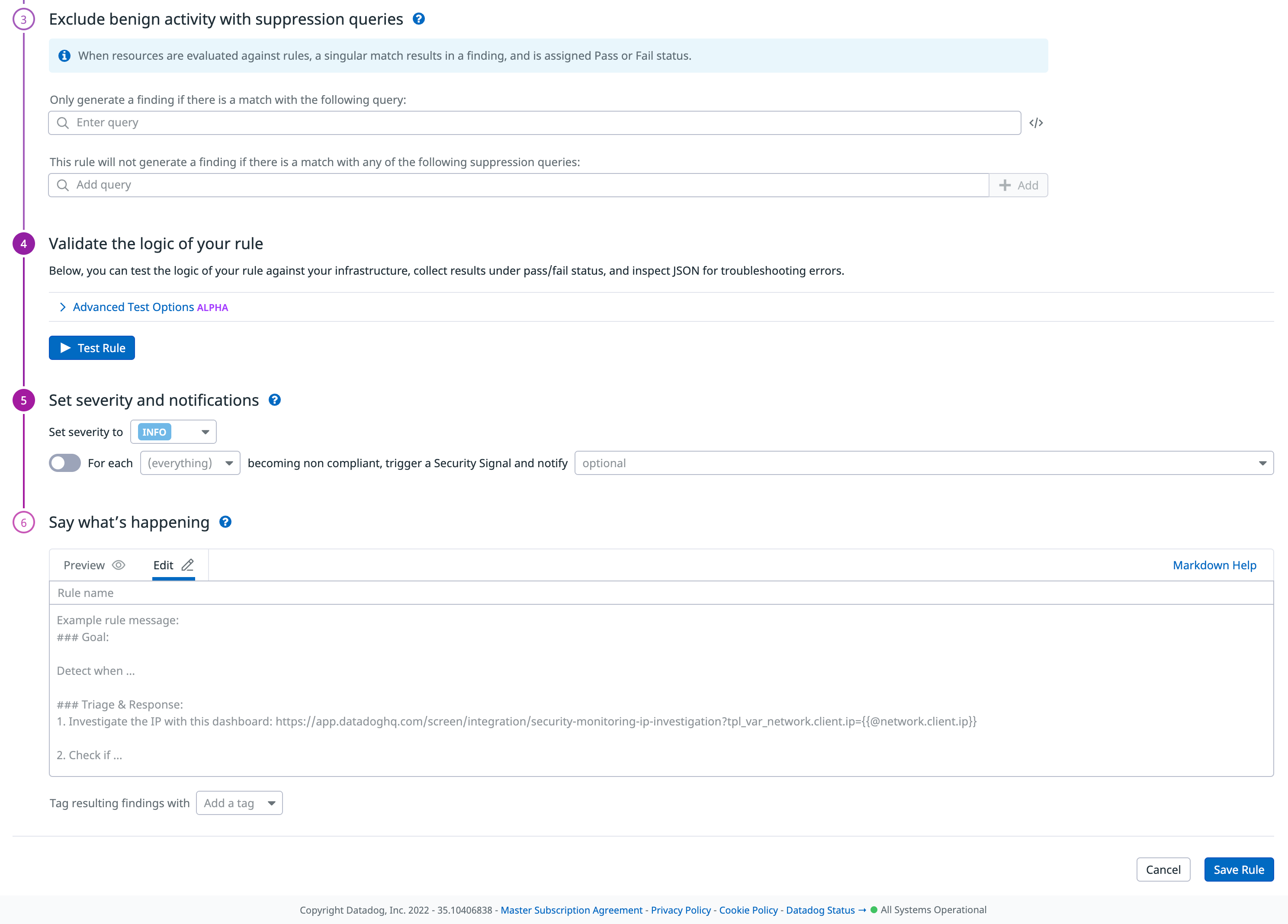
Exclude benign activity by specifying queries to include or remove certain resources from misconfigurations.
Validate the logic of your rule by selecting resources and clicking Test Rule. See which resources passed and failed, along with corresponding resource tags.
Specify a severity (
Critical,High,Medium,Low, orInfo) for the rule.Select a facet (for example, for each resource type or for each account ID), and specify a notification target to signal.
In Say what’s happening, write a description for the notification, using notification options to make it useful. Read Notifications for details.
Specify tags to apply to the result misconfigurations. Read Tagging misconfigurations for more information.
Click Save Rule.
Tagging misconfigurations
When you create, clone, or modify CSM Misconfigurations compliance rules, you can specify tags to apply to misconfigurations so that you can group, filter, and search misconfigurations by those tags. When you clone a rule, some tags are carried forward into the new rule, and others are not (see table below).
You can assign almost any key-value as a tag. The following table shows tags that are useful in common security scenarios.
| Key | Valid values | Description |
|---|---|---|
scored | true, false | Indicates whether to include the rule when calculating organization’s overall posture score. Automatically added to cloned rules. |
security | compliance | Categorizes misconfigurations on the Security Signals page. Can’t be removed. |
requirement | String | Not allowed for custom rules. Indicates a requirement related to a compliance framework. Don’t add this to rules not part of a compliance framework. |
cloud_provider | aws, gcp, azure | Cannot be removed. Is set automatically based on resource type. |
control | String | Not allowed for custom rules. Indicates a control related to a compliance framework. Don’t add this to rules not part of a compliance framework. |
source | String from a defined set given by cloud providers as listed in the Source facet in the Misconfigurations Explorer. | Cannot be removed. Automatically added to cloned rules. Facilitates grouping rules by cloud provider. |
framework | String | Not allowed for custom rules. Indicates the compliance framework the rule belongs to. Not automatically added to cloned rules. |
Further reading
Additional helpful documentation, links, and articles: