- 重要な情報
- はじめに
- Datadog
- Datadog サイト
- DevSecOps
- AWS Lambda のサーバーレス
- エージェント
- インテグレーション
- コンテナ
- ダッシュボード
- アラート設定
- ログ管理
- トレーシング
- プロファイラー
- タグ
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic モニタリング
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- Learning Center
- Support
- 用語集
- Standard Attributes
- ガイド
- インテグレーション
- エージェント
- OpenTelemetry
- 開発者
- 認可
- DogStatsD
- カスタムチェック
- インテグレーション
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- UI Extensions
- サービスのチェック
- IDE インテグレーション
- コミュニティ
- ガイド
- API
- CoScreen
- Cloudcraft
- アプリ内
- Service Management
- インフラストラクチャー
- アプリケーションパフォーマンス
- APM
- Continuous Profiler
- データベース モニタリング
- ユニバーサル サービス モニタリング
- Data Streams Monitoring
- Data Jobs Monitoring
- Software Delivery
- ログ管理
- セキュリティ
- セキュリティの概要
- Cloud SIEM
- クラウド セキュリティ マネジメント
- Application Security Management
- Digital Experience
- RUM & セッションリプレイ
- Synthetic モニタリング
- Continuous Testing
- Mobile Application Testing
- 管理
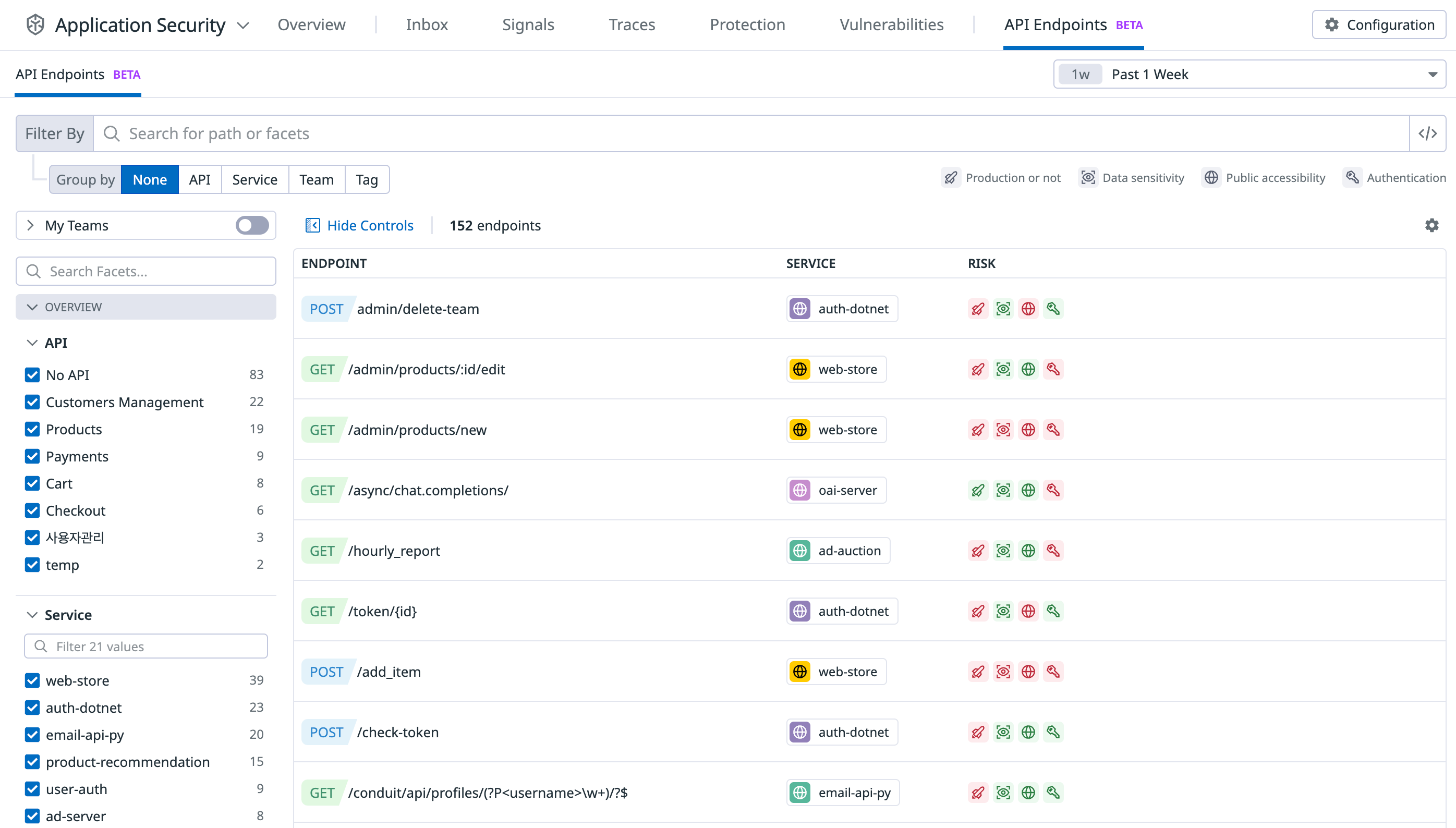
API Security Inventory
このページは日本語には対応しておりません。随時翻訳に取り組んでいます。翻訳に関してご質問やご意見ございましたら、お気軽にご連絡ください。
Overview
API Security Inventory monitors your API traffic to provide visibility into the security posture of your APIs, including:
- Authentication: Type of authentication used, such as Basic Auth and API key.
- Public Exposure: Whether the API is processing traffic from the internet.
- Production status: If the API is running in a production environment.
- Sensitive data flows: Sensitive data handled by the API and flows between APIs.
- Attack Exposure: If the endpoint is targeted by attacks (powered by Application Threat Management).
- Vulnerabilities: If the endpoint contains a vulnerability (powered by Software Composition Analysis).
Using the API Security Inventory you can:
- See at a glance your publicly exposed endpoints that are not requiring authenticated requests.
- See at a glance your publicly exposed endpoints that are handling sensitive data, such as payment card numbers.
- See which endpoints are at risk, and pivot directly into the Threat Monitoring and Protection service for further investigation or response.
Configuration
The following library versions are compatible with API Security Inventory. Remote Configuration is required.
| Technology | Minimum version | Support for sensitive data scanning |
|---|---|---|
| Python | v2.1.6 | Requests and responses |
| Java | v1.31.0 | Requests only |
| PHP | v0.98.0 | Requests and responses |
| .NET Core | v2.42.0 | Requests and responses |
| .NET Fx | v2.47.0 | Requests and responses |
| Ruby | v1.15.0 | Requests only |
| Golang | v1.59.0 | Requests only |
| Node.js | v3.51.0, v4.30.0 or v5.6.0 | Requests and responses |
How it works
API Inventory leverages the Datadog tracing library with ASM enabled to gather security metadata about API traffic, including the API schema, types of sensitive data processed, and the authentication scheme.
API Inventory Security uses Remote Configuration to manage and configure scanning rules that detect sensitive data and authentication.
The following risks are calculated for each endpoint:
Service in production
The env tag is checked for patterns that frequently represent non-production environments. For example, if it detects values of dev, alpha, beta, sandbox, or similar, it marks the environment as non-production. All other environments are marked as production.
Service under attack
This risk is detected for API endpoints that have experienced attacks within the last week.
Processing sensitive data
ASM matches known patterns for sensitive data in API requests. If it finds a match, the endpoint is tagged with the type of sensitive data processed.
The matching occurs within your application, and none of the sensitive data is sent to Datadog.
Supported data types
| Category | Category facet | Type facet |
|---|---|---|
| Canadian social insurance numbers | pii | canadian_sin |
| United States social security numbers | pii | us_ssn |
| UK national insurance numbers | pii | uk_nin |
| US vehicle identification numbers | pii | vin |
| Passport numbers | pii | passport_number |
| E-mail addresses | pii | email |
| JSON Web Token (JWT) | credentials | json_web_token |
Bearer tokens (found in Authorization headers) | credentials | bearer_token |
| American Express card number | payment | card |
| Diners Club card number | payment | card |
| JCB card number | payment | card |
| Maestro card number | payment | card |
| Mastercard card number | payment | card |
| VISA card number | payment | card |
| IBAN bank account number | payment | iban |
Publicly accessible
Datadog marks an endpoint as public if the client IP address is outside these ranges:
- 10.0.0.0/8
- 172.16.0.0/12
- 192.168.0.0/16
- 169.254.1.0/16
See Configuring a client IP header for more information on the required library configuration.
Unauthenticated endpoint
Authentication is determined by:
- The presence of
Authorization,TokenorX-Api-Keyheaders. - The presence of a user ID within the trace (for example, the
@usr.idAPM attribute). - The request has responded with a 401 or 403 status code.
Contains exploitable vulnerabilities
This risk is determined by Software Composition Analysis for the service hosting the endpoint.
Performance impact
By default, API Security Inventory evaluates every tenth request (10% sample rate).
Further reading
お役に立つドキュメント、リンクや記事: