- Essentials
- Getting Started
- Datadog
- Datadog Site
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Integrations
- Containers
- Dashboards
- Monitors
- Logs
- APM Tracing
- Profiler
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic Monitoring
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Test Impact Analysis
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- OpenTelemetry
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- API
- Datadog Mobile App
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Sheets
- Monitors and Alerting
- Infrastructure
- Metrics
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Real User Monitoring
- Product Analytics
- Synthetic Testing and Monitoring
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Optimization
- Code Analysis
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
Code Analysis
Code Analysis is not available for the site.
Try the Beta!
Code Analysis is in public beta.
Overview
Datadog Software Composition Analysis can find vulnerable libraries across the software development lifecycle (SDLC). Code Analysis summarizes results found by directly scanning your repositories. To view all vulnerabilities found in repositories and at runtime consolidated together, see Application Security for more details.
Code Analysis scans your repositories to find security vulnerabilities and code quality issues. It encompasses two capabilities: Static Analysis for your first-party code, and Software Composition Analysis (SCA) for open-source dependencies in your codebase.
- Static Analysis
- Scans your bespoke code for maintainability issues, bugs, performance issues, and security vulnerabilities early in the development lifecycle to catch issues from reaching production and, when possible, provide suggested fixes to help engineering teams address these issues before they impact users.
- Software Composition Analysis
- Scans the open source libraries that are imported into your repositories for known security vulnerabilities, license risks, and end-of-life libraries.
Set up Code Analysis on your repository
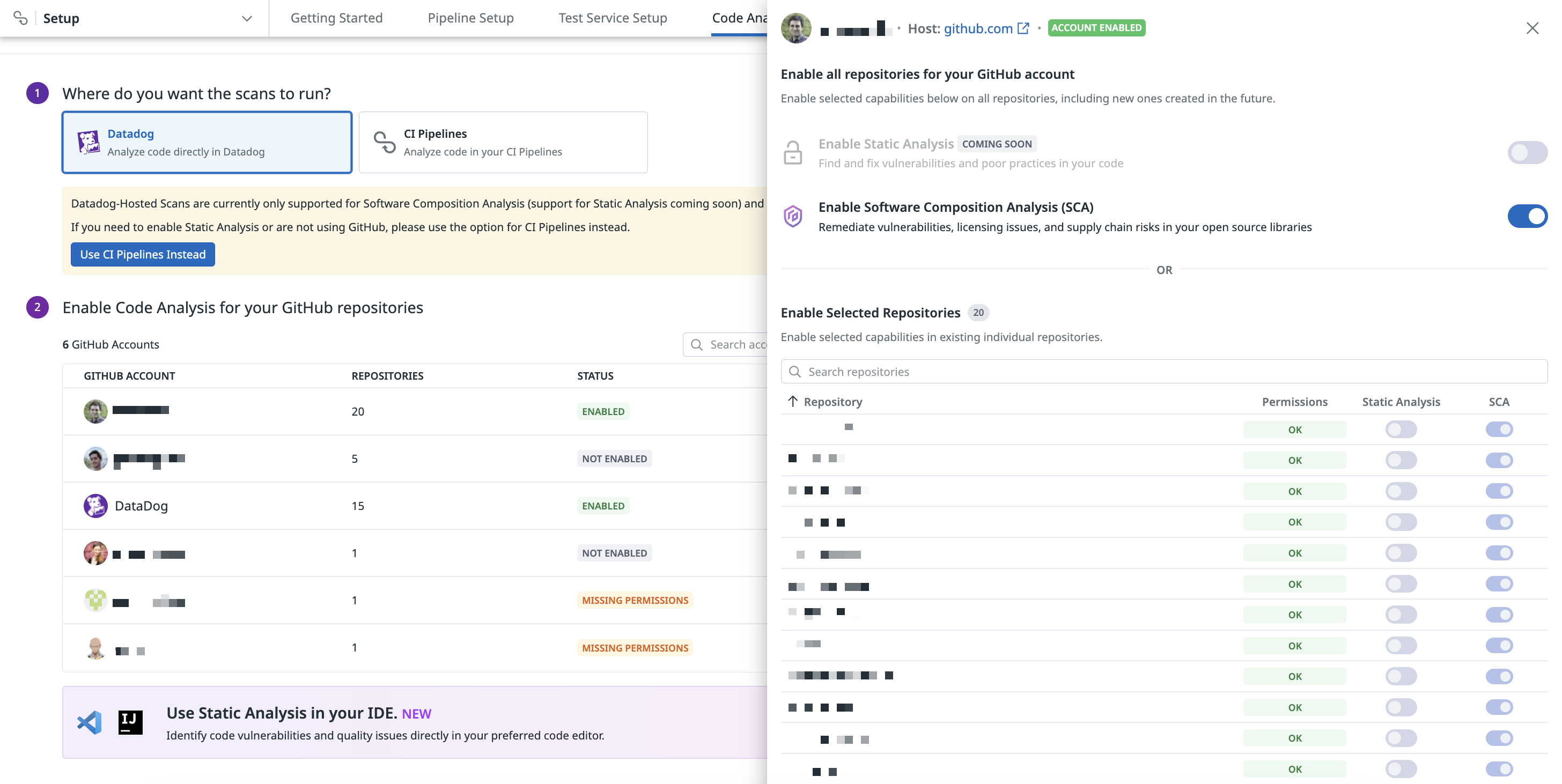
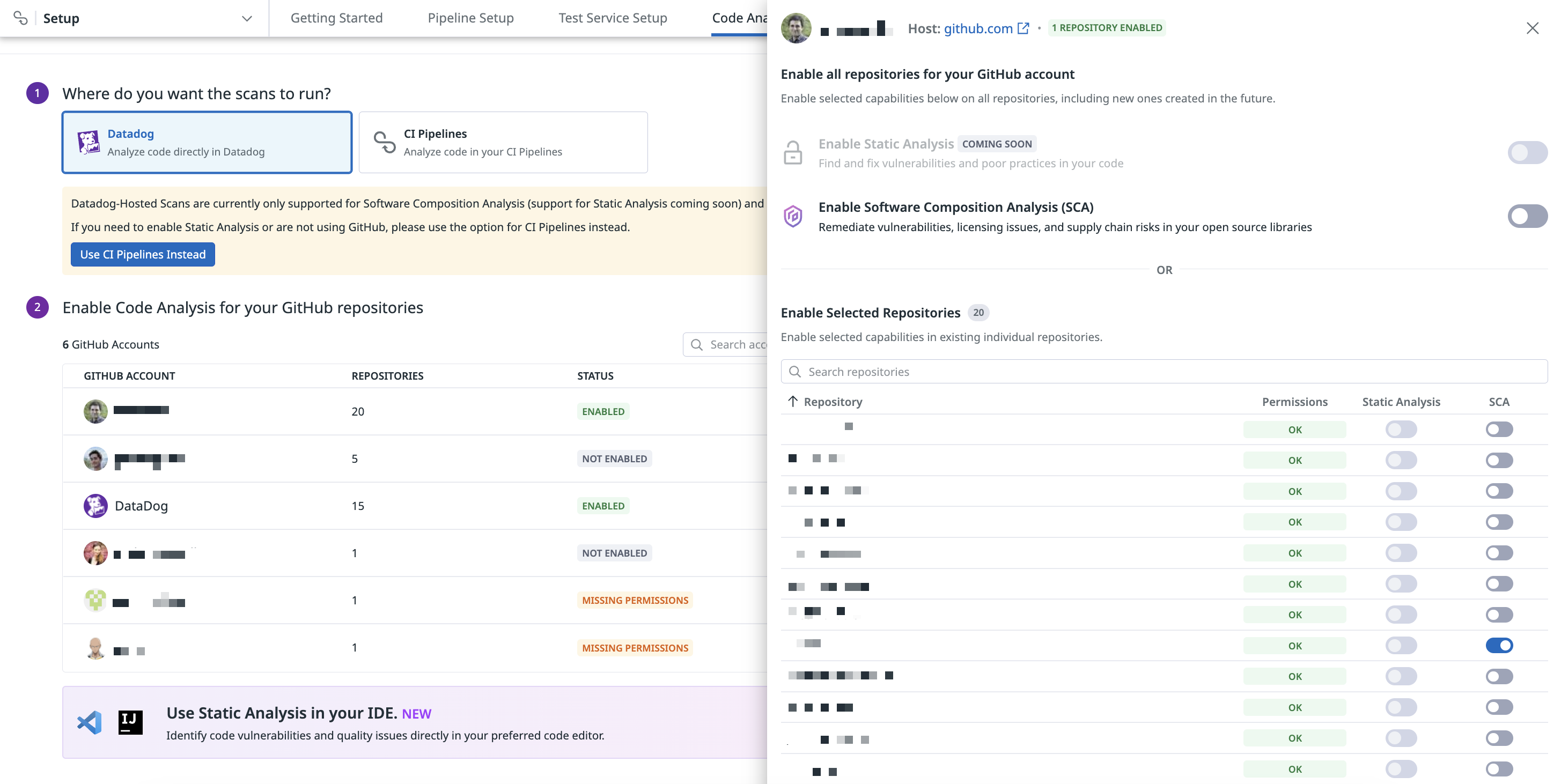
Click + Add a Repository on the Code Analysis Repositories page and choose to run the scans directly in Datadog or in your CI pipelines.
Datadog-hosted scans are supported by Software Composition Analysis (SCA) and GitHub repositories only. To enable Static Analysis or use a different CI provider, run scans in your CI pipelines instead.
With Datadog-hosted scans, your code is scanned within Datadog’s infrastructure as opposed to within your CI pipeline. Datadog reads your code, runs the static analyzer to perform Static Analysis and/or Software Composition Analysis, and uploads the results.
Using Datadog-hosted scans eliminates the need for you to configure a CI pipeline so you can use Code Analysis.
To enable Software Composition Analysis on GitHub repositories, click Select Repositories on your desired GitHub account and click the toggle for Enable Software Composition Analysis (SCA) to enable for all repositories. If you don’t see any GitHub accounts listed, create a new GitHub App to get started.
Optionally, you can select specific GitHub repositories to enable SCA by clicking the toggle for each repository.
If you do not want to run your scans directly through Datadog, you can select which scans you’d like to run (Static Analysis and Software Composition Analysis) and configure your CI pipeline provider accordingly.
Configure your CI/CD provider
See the following documentation to configure your CI/CD provider to run Static Analysis and SCA scans:
Set up the GitHub integration
You can configure a GitHub App by using the GitHub integration tile and setting up the source code integration to see the offending code snippets as part of the Static Analysis results in Datadog.
For more information, see the Source Code Integration documentation.
Static Analysis integrations
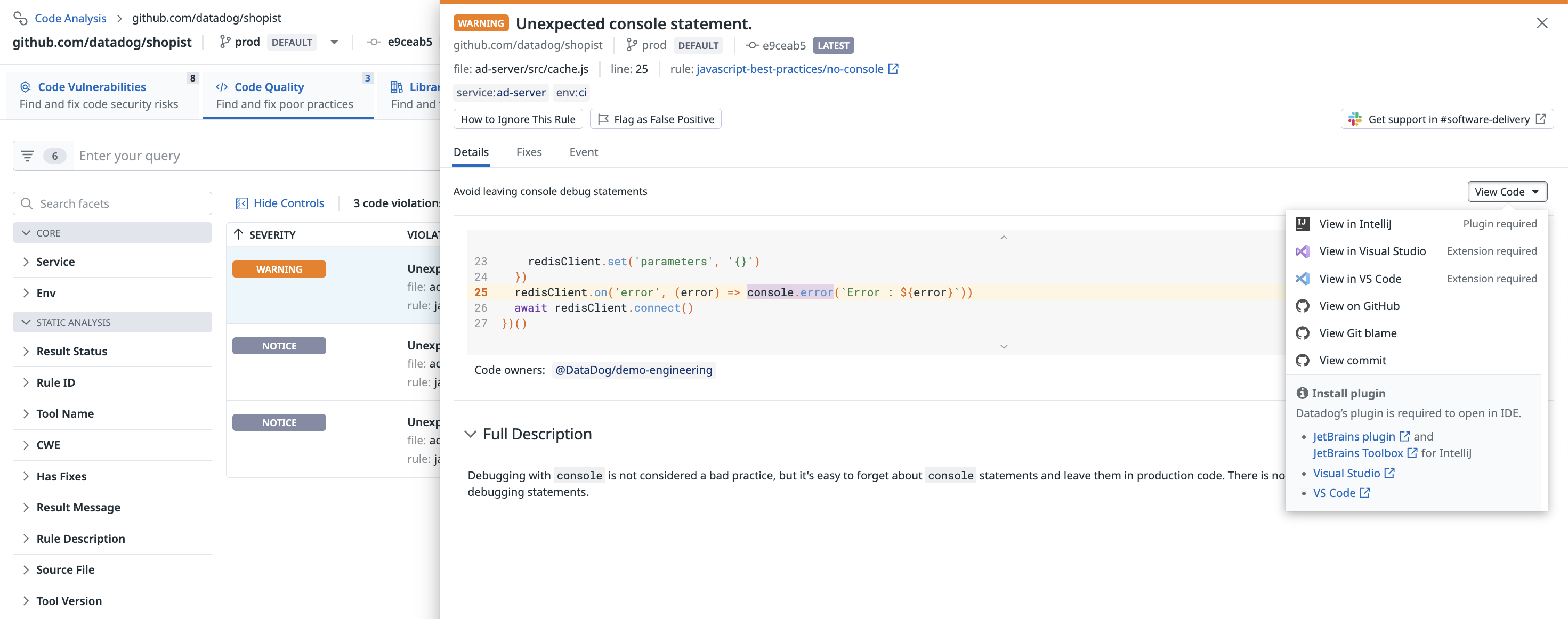
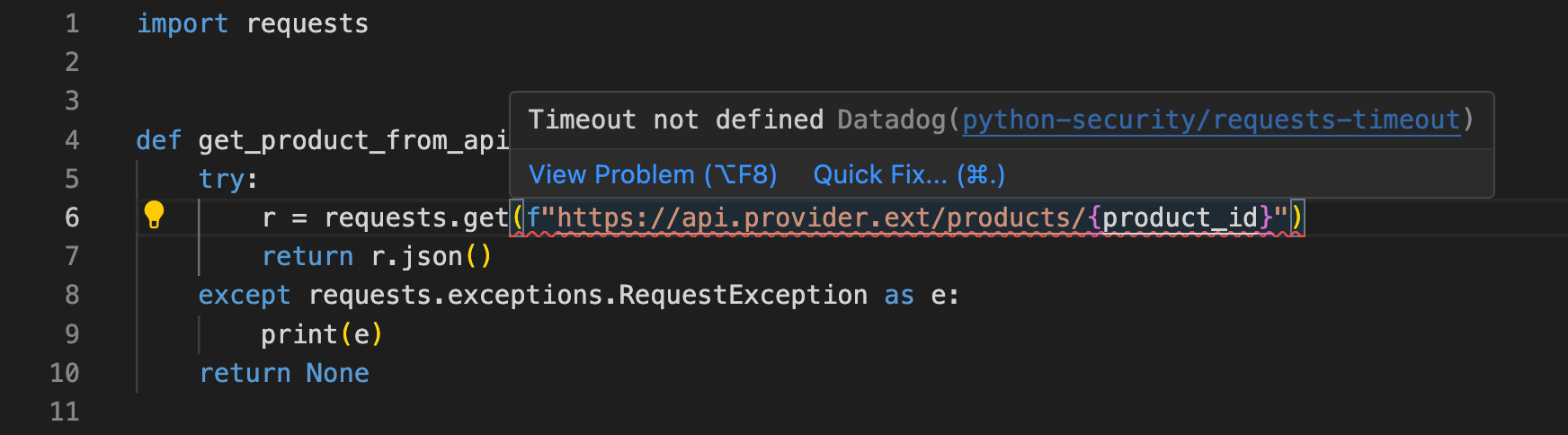
With Static Analysis, you can receive automated feedback on poor coding practices and security vulnerabilities on the code you write directly in an IDE such as VS Code or IntelliJ & PyCharm, and in your pull requests on GitHub.
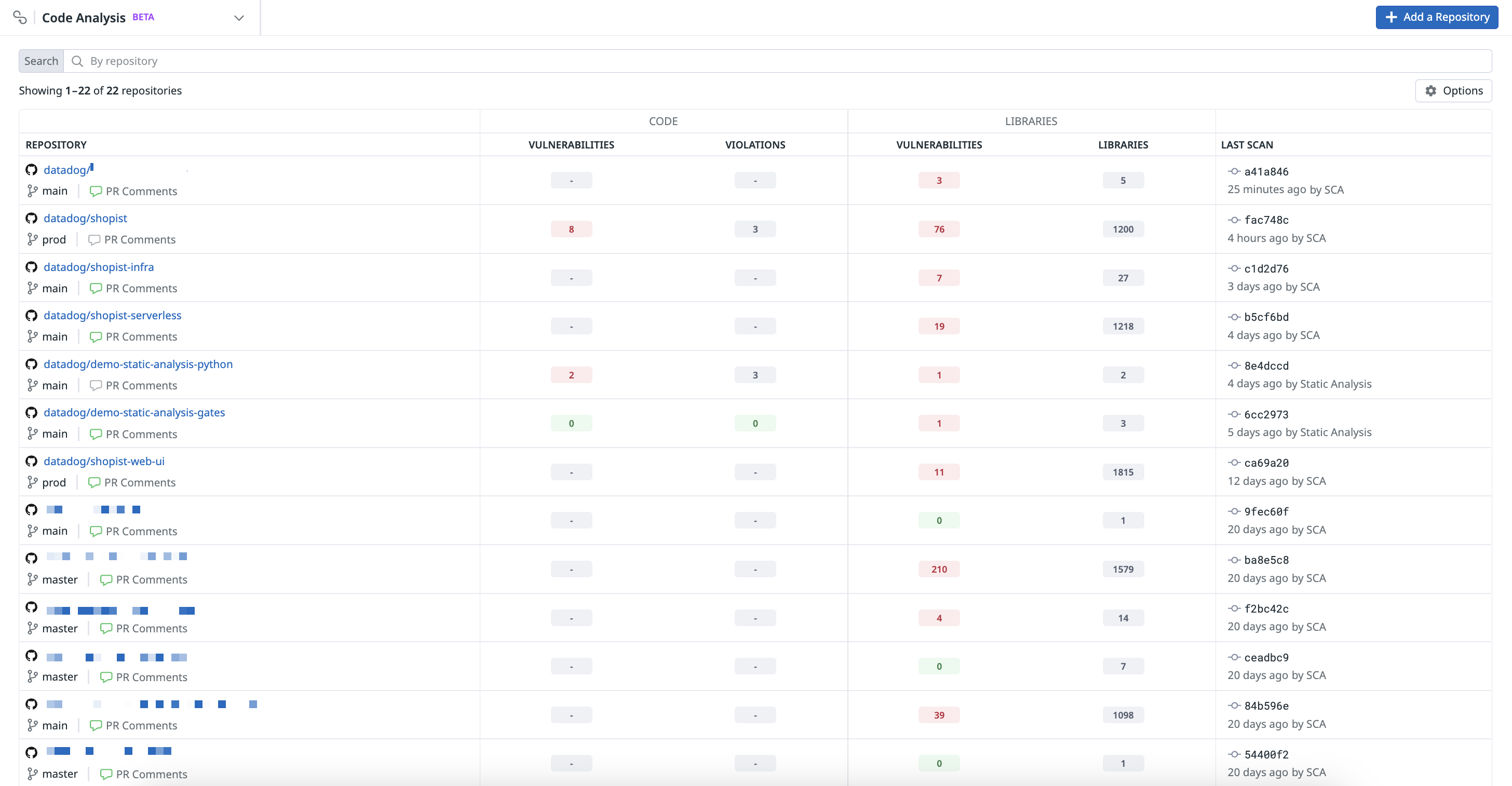
Search and manage repositories
After you have configured Code Analysis, you can see a summary of the results from the Static Analysis and SCA scans for each of your repositories on the Code Analysis page. By default, the summarized results are shown for the latest scanned commit on the default branch of the repository, which ensures that you are seeing all the existing problems on each repository that you may want to triage and fix.
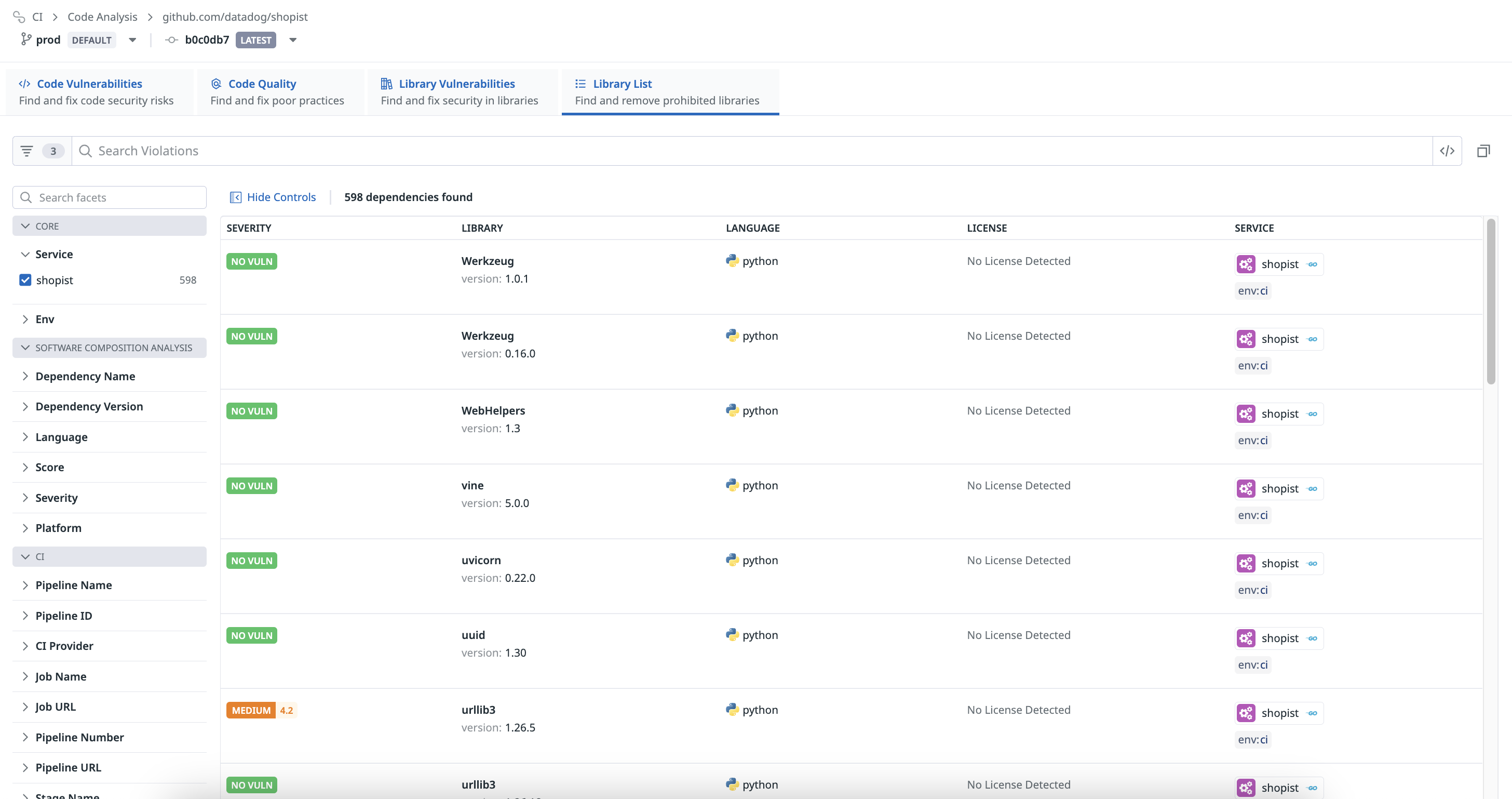
Select a repository from the list to search through and manage violations for that specific repository. By default, results are shown for the latest scanned commit on the default branch of the repository, but you may change the branch or commit at the top of the page. Results can also be filtered by service or team facets. For more information about how results are linked to Datadog services and teams, see Getting Started with Code Analysis.
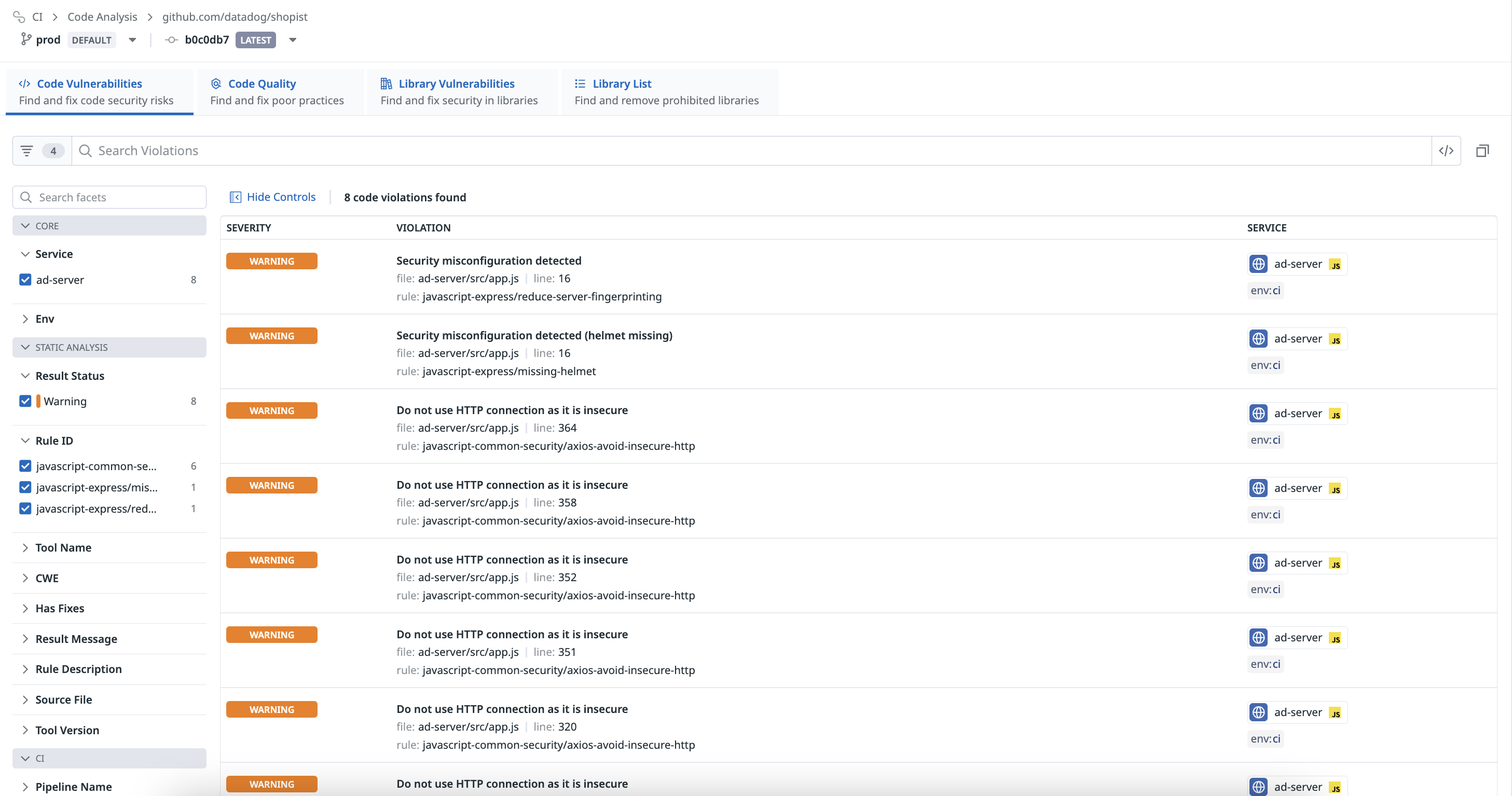
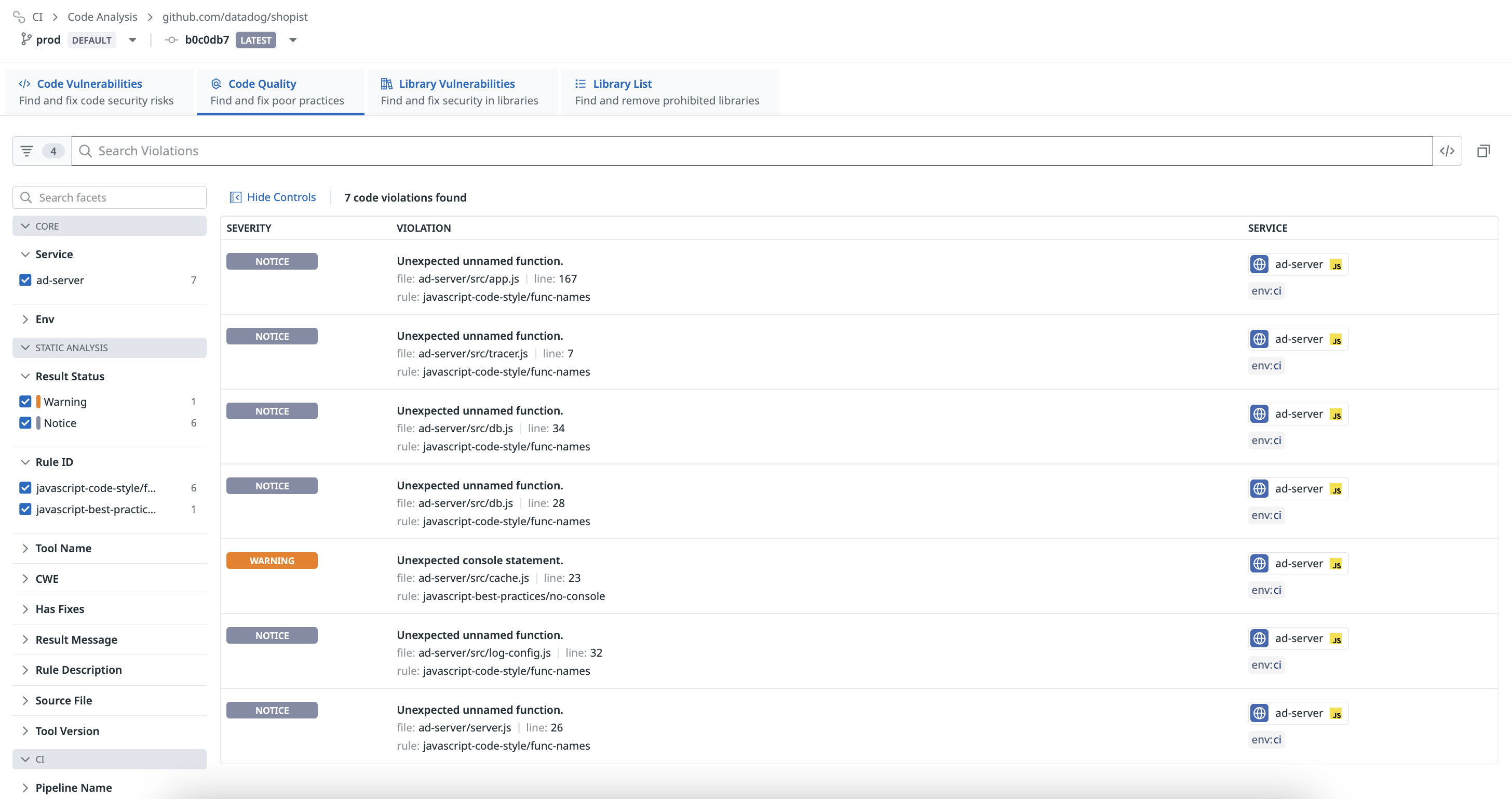
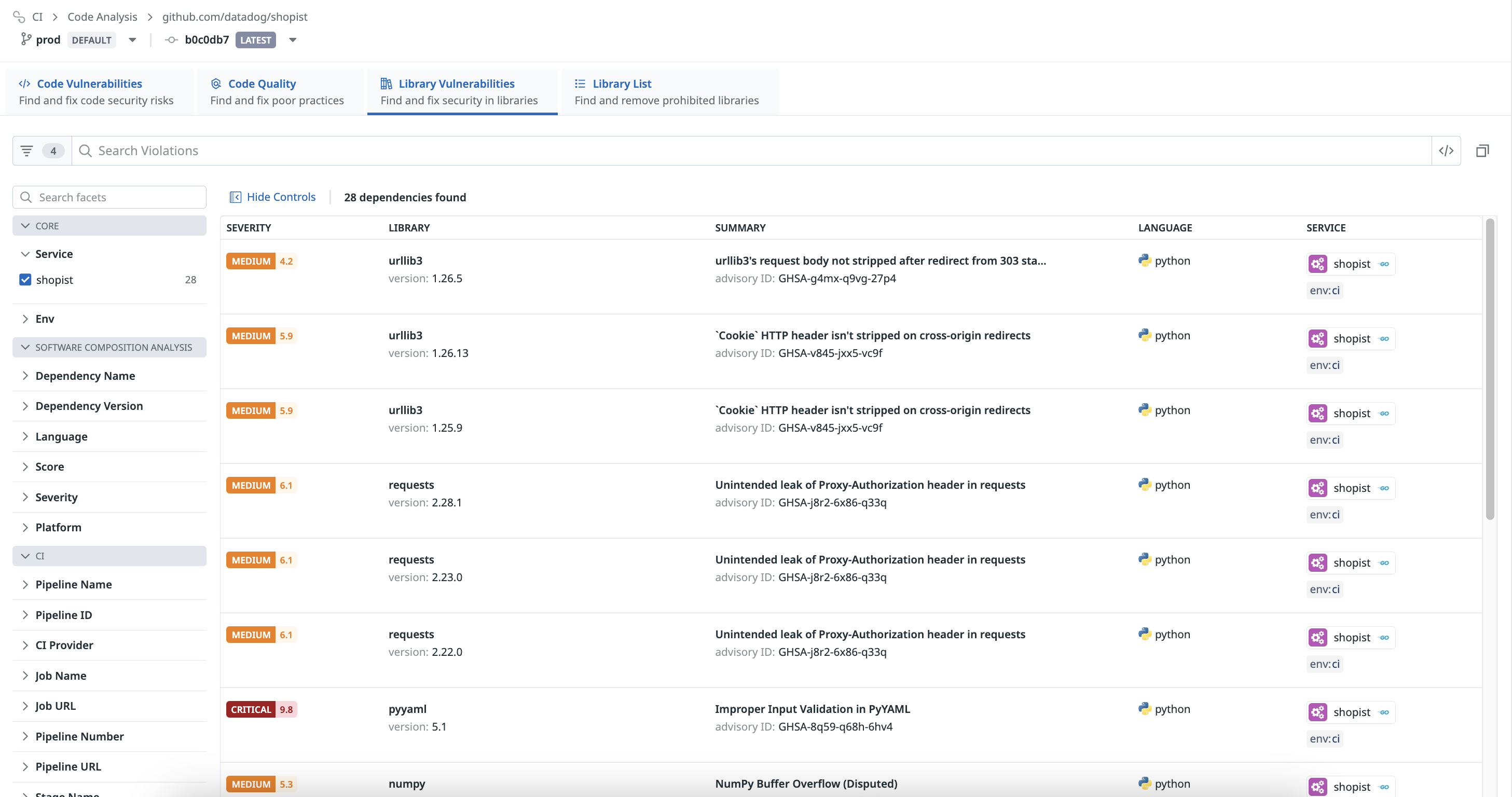
Regardless of the selected branch or commit, all results are organized into the following views:
Identify and address code security risks detected by Static Analysis in the Code Vulnerabilities view.
Identify and address poor coding practices detected by Static Analysis in the Code Quality view.
Identify and address vulnerable open source libraries detected by SCA in the Library Vulnerabilities view.
Manage the full list of libraries detected by SCA that have imported into your codebase in the Library Catalog view.
Further Reading
Additional helpful documentation, links, and articles: