- Principales informations
- Getting Started
- Datadog
- Site Datadog
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Intégrations
- Conteneurs
- Dashboards
- Monitors
- Logs
- Tracing
- Profileur
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Surveillance Synthetic
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Intégrations
- OpenTelemetry
- Développeurs
- Authorization
- DogStatsD
- Checks custom
- Intégrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Checks de service
- IDE Plugins
- Communauté
- Guides
- API
- Application mobile
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Alertes
- Infrastructure
- Métriques
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Universal Service Monitoring
- Conteneurs
- Sans serveur
- Surveillance réseau
- Cloud Cost
- Application Performance
- APM
- Profileur en continu
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Configuration de Postgres
- Configuration de MySQL
- Configuration de SQL Server
- Setting Up Oracle
- Setting Up MongoDB
- Connecting DBM and Traces
- Données collectées
- Exploring Database Hosts
- Explorer les métriques de requête
- Explorer des échantillons de requêtes
- Dépannage
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- RUM et Session Replay
- Product Analytics
- Surveillance Synthetic
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Visibility
- Exécuteur de tests intelligent
- Code Analysis
- Quality Gates
- DORA Metrics
- Securité
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Pipelines d'observabilité
- Log Management
- Administration
Exploit Prevention
Cette page n'est pas encore disponible en français, sa traduction est en cours.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Exploit Prevention is in public beta. See the library compatibility section for supported libraries.
Overview
Use ASM Exploit Prevention to protect your critical applications and APIs against zero-day vulnerabilities without tuning or reconfiguration.
With ASM’s context-aware capabilities, you can gain a deep understanding of application logic, data flow, and state.
Combine telemetry from the Datadog tracer with predefined heuristics to detect and block exploits with higher accuracy, ensuring legitimate traffic remains unaffected.
You can use ASM Exploit Prevention in the following use cases:
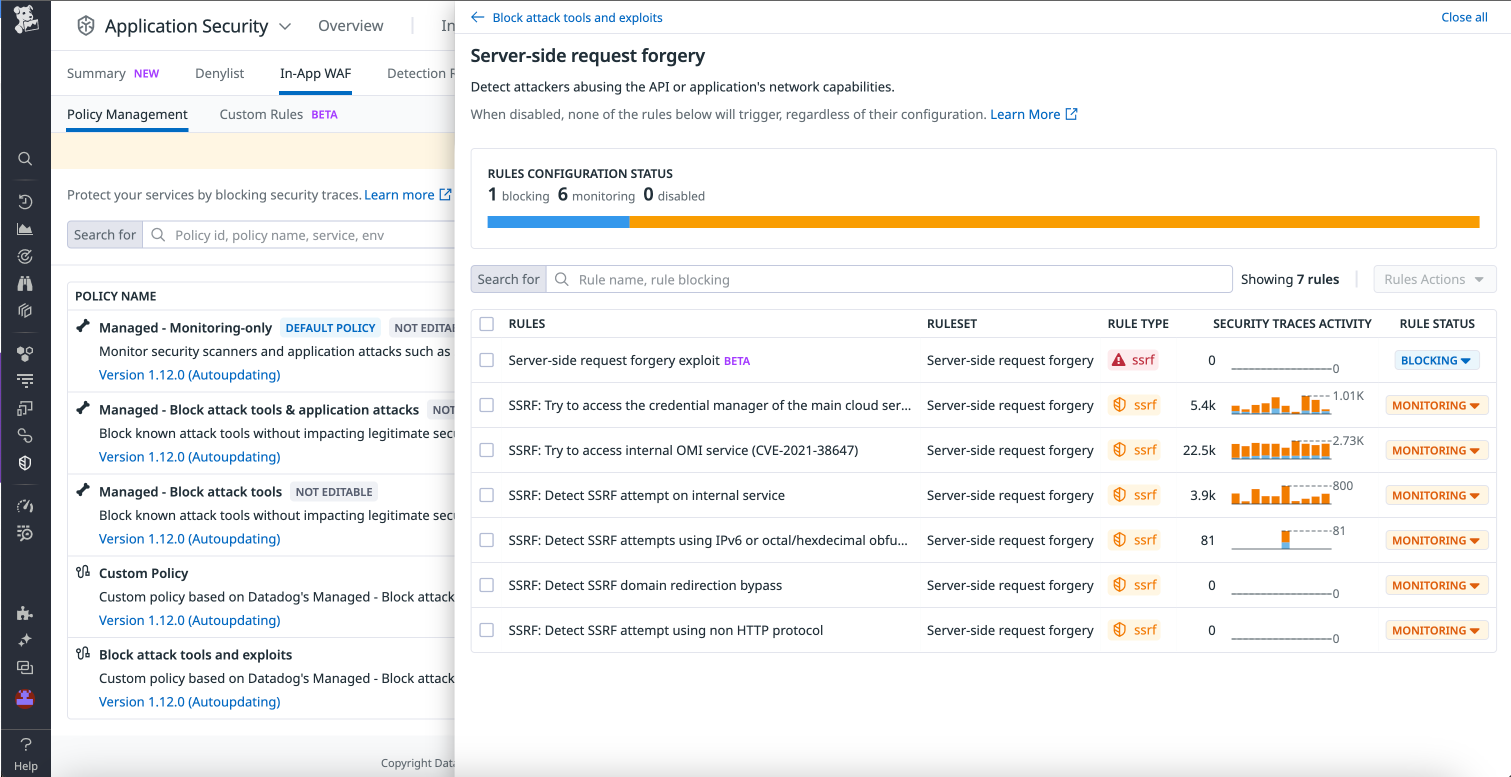
Example 1: Server-side request forgery
An attacker tricks the server into making unauthorized requests to internal systems or external servers, potentially leaking information or a further exploitation.
ASM Exploit Prevention checks whether an internal or external request’s URL, which is partially or totally controlled by a user parameter, has been manipulated by an attacker to alter the original purpose of the request.
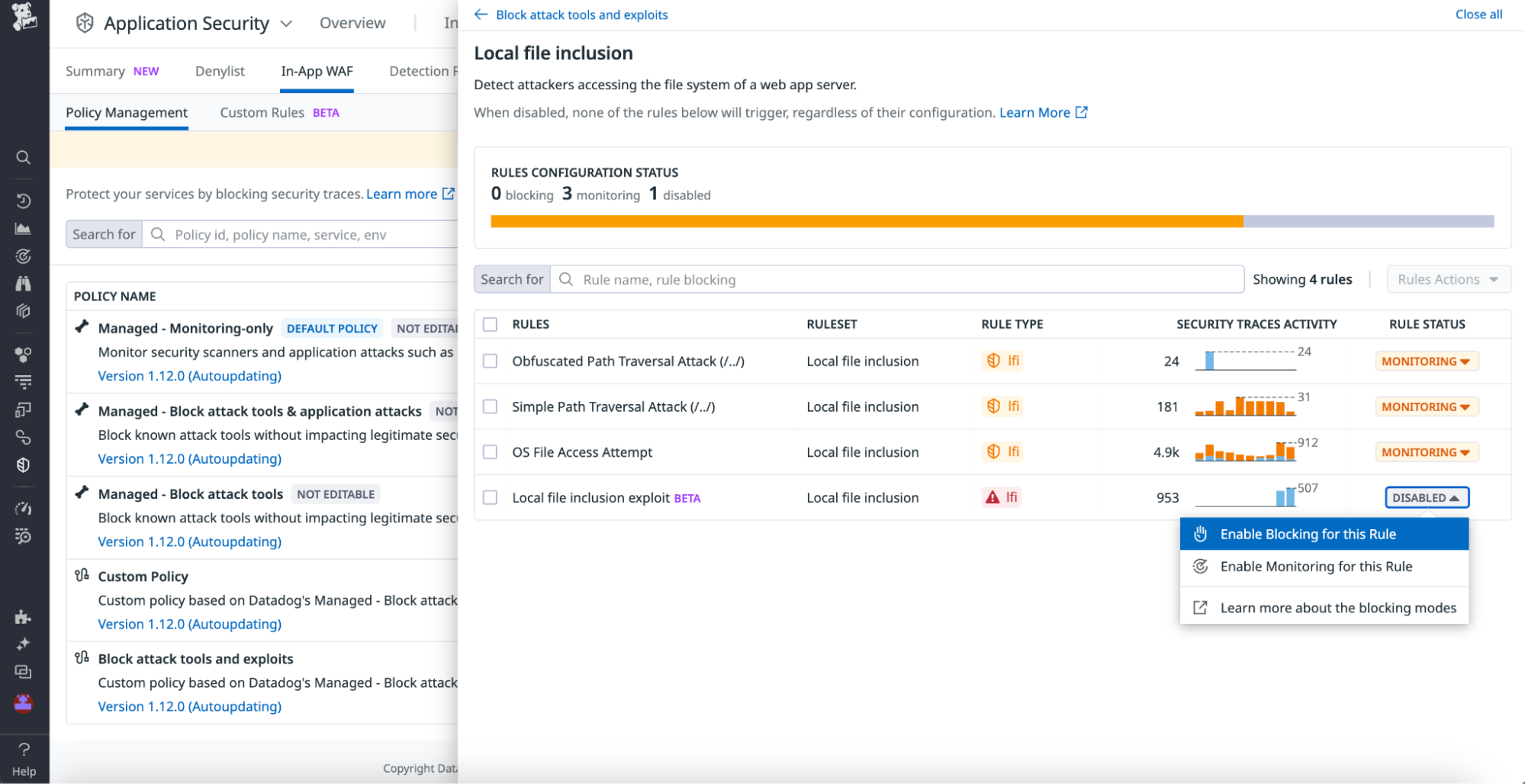
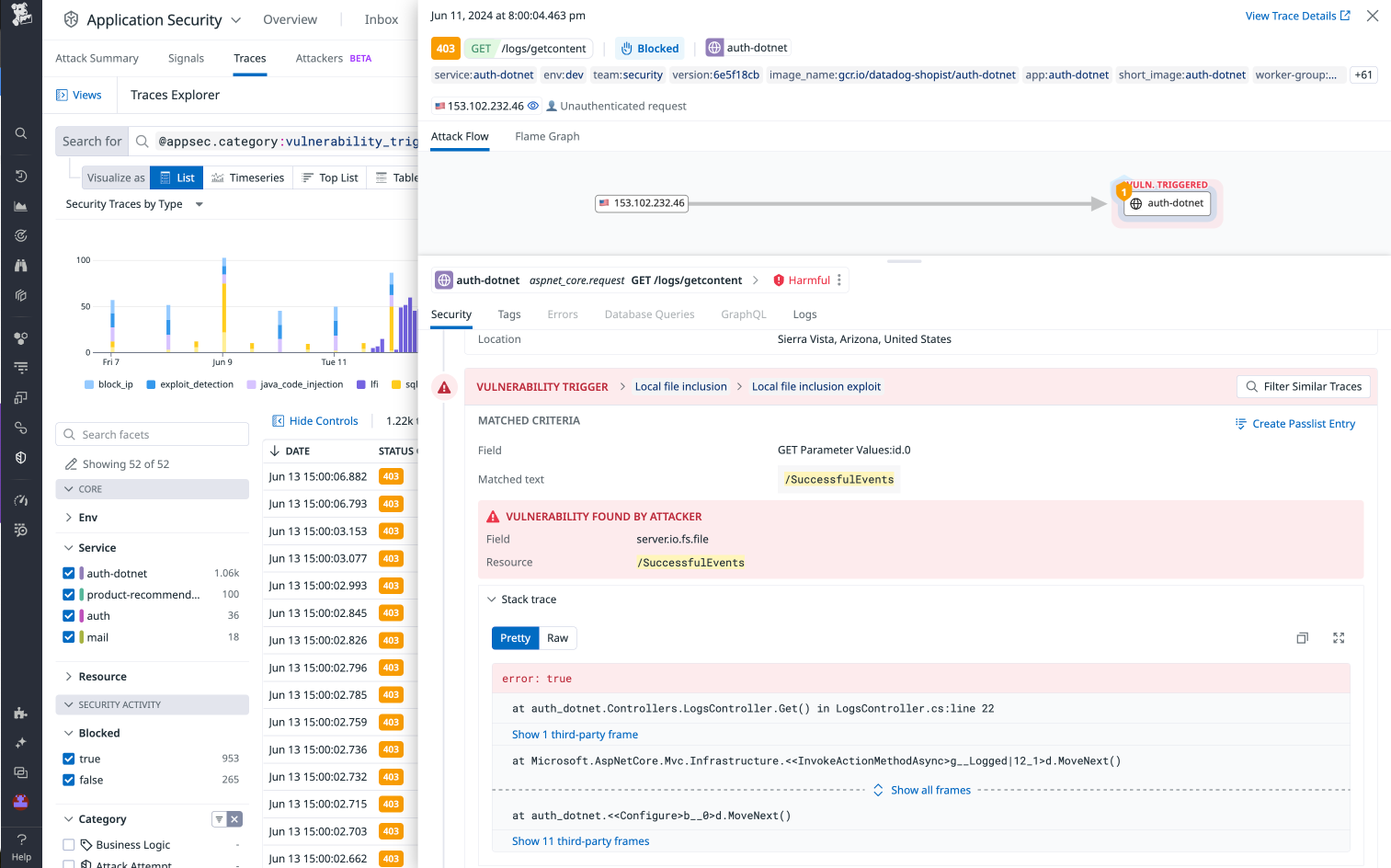
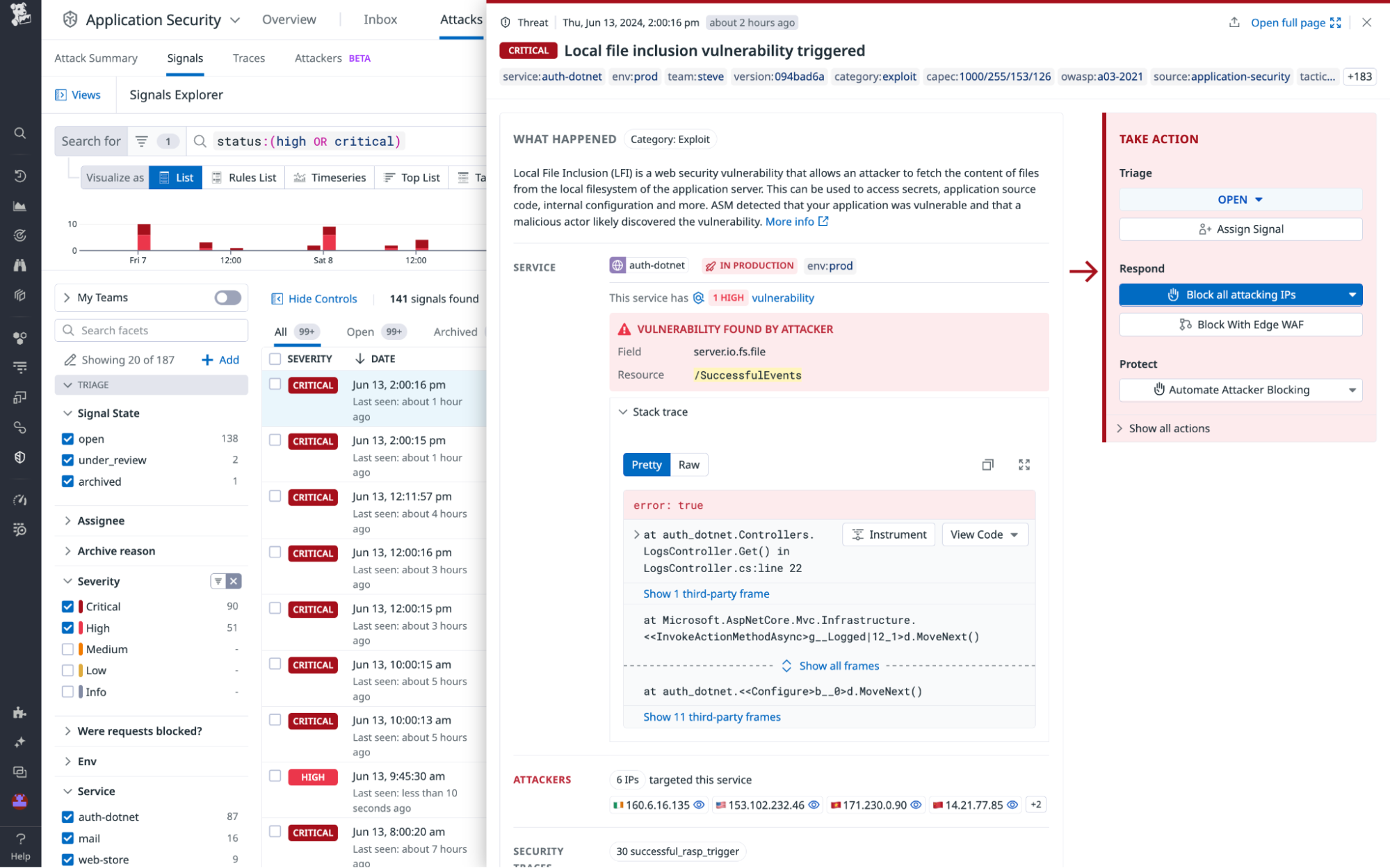
Example 2: Local file inclusion
An attacker exploits a vulnerable parameter to include local files from the server, potentially exposing sensitive data like configuration files or possibly enabling remote code execution.
ASM Exploit Prevention inspects all file access attempts to determine if the path has been injected and whether a restricted file is accessed.
Example 3: SQL injection
An attacker injects malicious SQL code into a query, potentially gaining unauthorized access to the database, manipulating data, or executing administrative operations.
ASM Exploit Prevention intercepts all SQL queries to determine if a user parameter has been injected and whether the injection alters the original purpose and structure of the SQL query.
Prerequisites
- Ensure that your applications are instrumented with the Datadog tracer.
- ASM Threat Management must be enabled. See Threat Management Setup.
- Ensure Remote Configuration is enabled to push rule updates and In-App WAF policies. See Enabling Remote Configuration.
Library Compatibility
| Exploit Type | .NET | Python | Go | Java | Node.js | PHP |
|---|---|---|---|---|---|---|
| Server-side Request Forgery (SSRF) | v2.53.0 | v2.9.0 | v1.65.0 | v1.39.0 | v5.20.0, v4.44.0 | Avail. in Q4 ‘24 |
| Local File Inclusion (LFI) | v3.4.0 | v2.9.0 | orchestrion v0.8.0 | v1.40.0 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 |
| SQL Injection (SQLi) | v3.4.0 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 |
| Command Injection | v3.2.0 | v2.11.0 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 | Avail. in Q4 ‘24 |
Note: Estimated availability of Exploit Prevention support for Ruby is Q4 ‘24.
Enabling Exploit Prevention
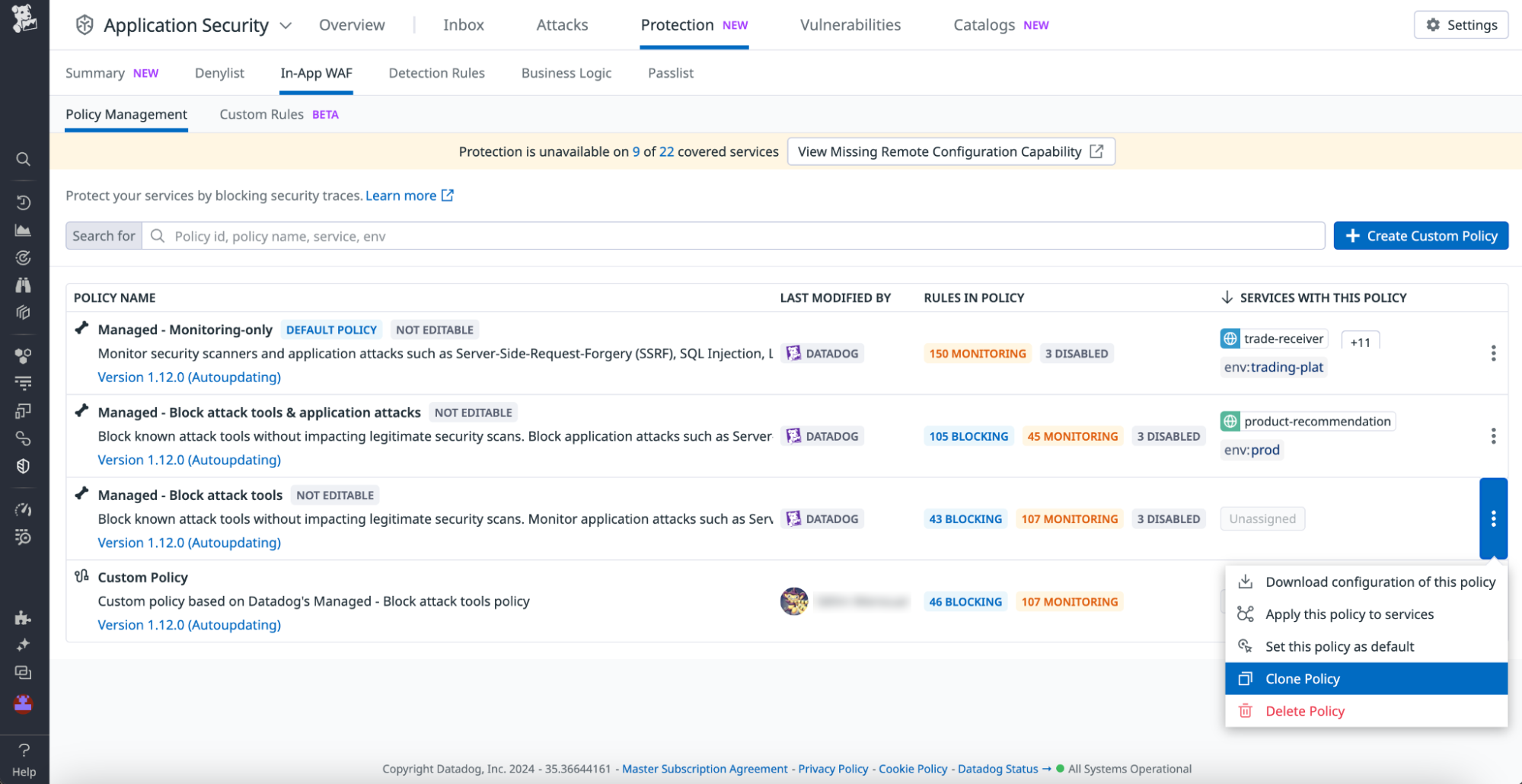
Navigate to In-App WAF (Security > Application Security > Protection > In-App WAF).
If you have applied a Datadog managed policy to your services, then follow these steps:
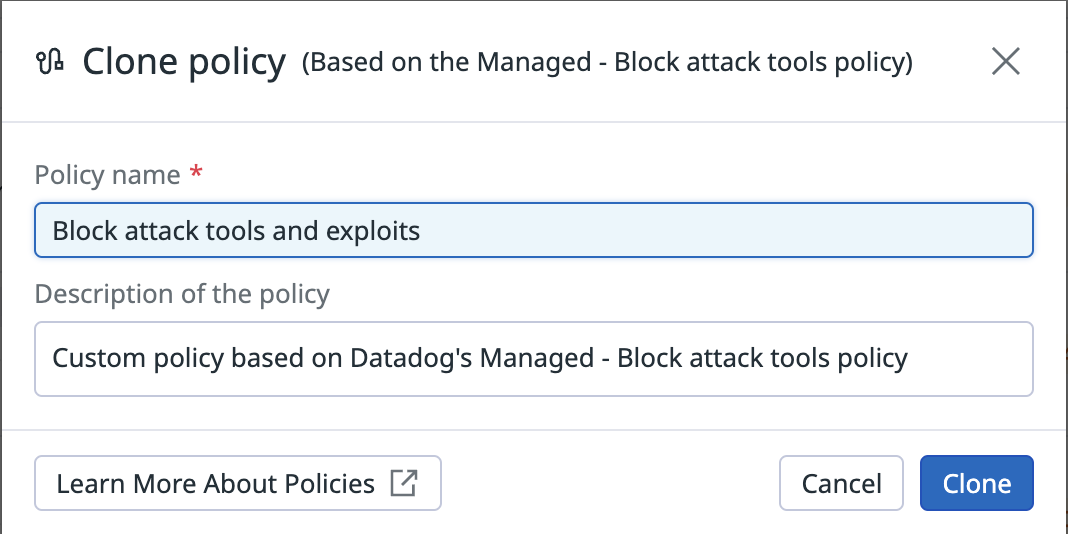
b. Add a policy name and description.c. Click on the policy you created and select the Local File Inclusion ruleset. Enable blocking for the Local File Inclusion exploit rule.d. Similarly, select the Server-side Request Forgery ruleset and enable blocking for the Server-side request forgery exploit rule.
a. Clone the policy. For example, you can use the Managed - Block attack tools policy.If you have applied a custom policy for your services, you can skip Steps 2.a and 2.b for cloning a policy and directly set the Exploit Prevention rules in blocking mode (Steps 2.c and 2.d).
Reviewing exploit attempts in ASM
After you have enabled Exploit Prevention, if ASM detects an exploit attempt, it proceeds to block that request. Exploit Prevention detections are always accompanied by stack traces, which provide full visibility of where the vulnerability lies in your code, ensuring a clear path to remediation.
In addition, ASM also generates a signal correlating all the blocked traces and isolating the attacker IP addresses that are targeting your service(s). You can take action by blocking all attacking IPs.
Further Reading
Documentation, liens et articles supplémentaires utiles: