- Essentials
- Getting Started
- Datadog
- Datadog Site
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Integrations
- Containers
- Dashboards
- Monitors
- Logs
- APM Tracing
- Profiler
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic Monitoring
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Test Impact Analysis
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- OpenTelemetry
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- Administrator's Guide
- API
- Datadog Mobile App
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Sheets
- Monitors and Alerting
- Infrastructure
- Metrics
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Real User Monitoring
- Product Analytics
- Synthetic Testing and Monitoring
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Optimization
- Code Analysis
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
Kubernetes Security Posture Management
Kubernetes Security Posture Management (KSPM) for Cloud Security Management (CSM) helps you proactively strengthen the security posture of your Kubernetes deployments by benchmarking your environment against established industry best practices, such as those defined by CIS, or your own custom detection policies.
Setting up KSPM
To take full advantage of KSPM, you must install both the Datadog Agent and cloud integrations. For detailed instructions, see the following articles:
- CSM Enterprise (Agent and cloud integrations)
- CSM Pro (Agent and cloud integrations)
This allows Datadog to detect risks in your Kubernetes deployments for each of the following resource types:
| Resource Type | Install Method | Framework |
|---|---|---|
aws_eks_cluster | cloud integration | cis-eks |
aws_eks_worker_node | Agent | cis-eks |
azure_aks_cluster | cloud integration | cis-aks |
azure_aks_worker_node | Agent | cis-aks |
kubernetes_master_node | Agent | cis-kubernetes |
kubernetes_worker_node | Agent | cis-kubernetes |
Monitor risk across Kubernetes deployments
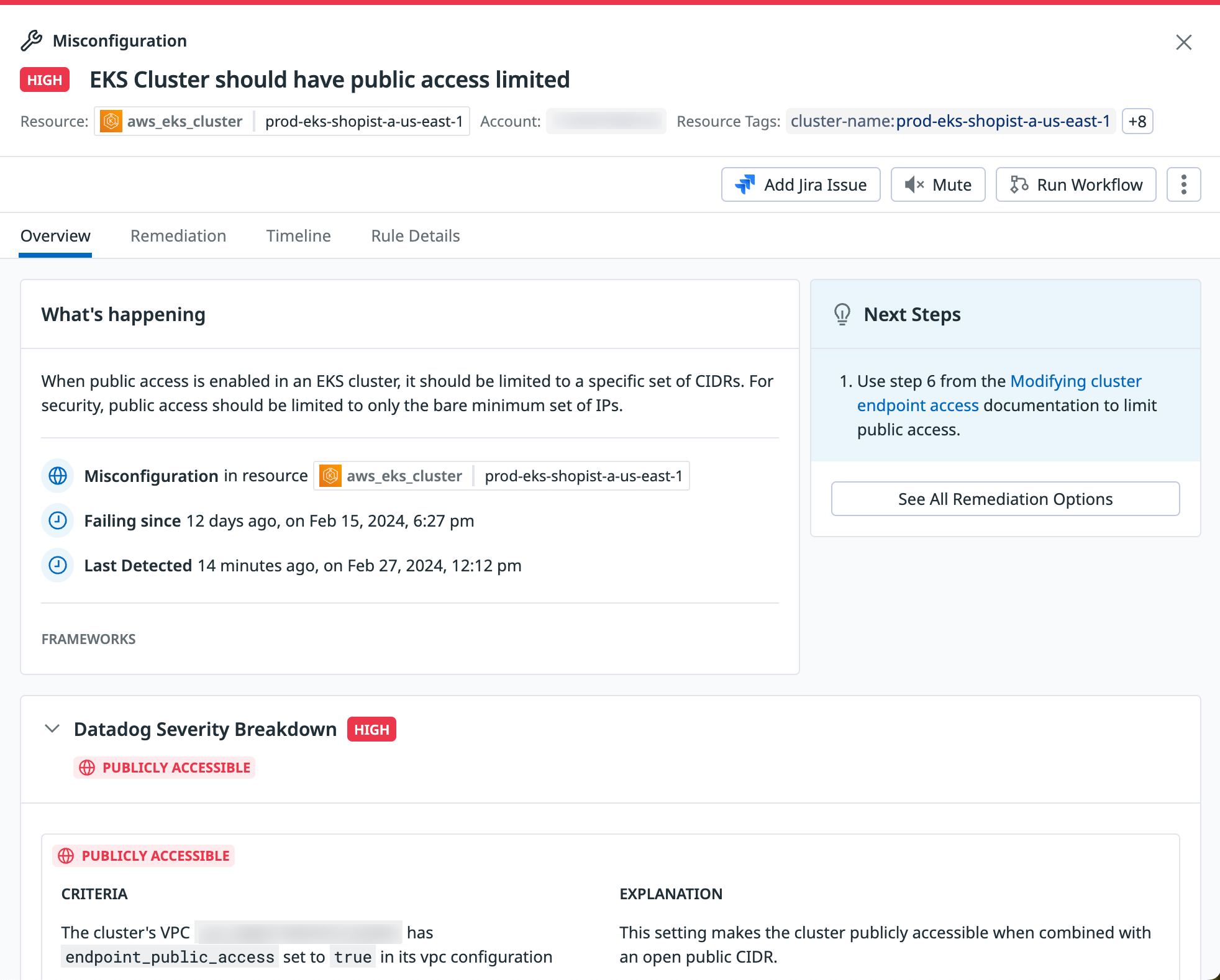
With KSPM, Datadog scans your environment for risks defined by more than 50+ out-of-the-box Kubernetes detection rules. When at least one case defined in a rule is matched over a given period of time, a notification alert is sent, and a finding is generated in the Misconfigurations Explorer.
Each finding contains the context you need to identify the issue’s impact, such as the full resource configuration, resource-level tags, and a map of the resource’s relationships with other components of your infrastructure. After you understand the problem and its impact, you can start remediating the issue by creating a Jira ticket from within CSM or by executing a pre-defined workflow.
Note: You can also use the API to programmatically interact with findings.
Assess your Kubernetes security posture against industry-standard frameworks
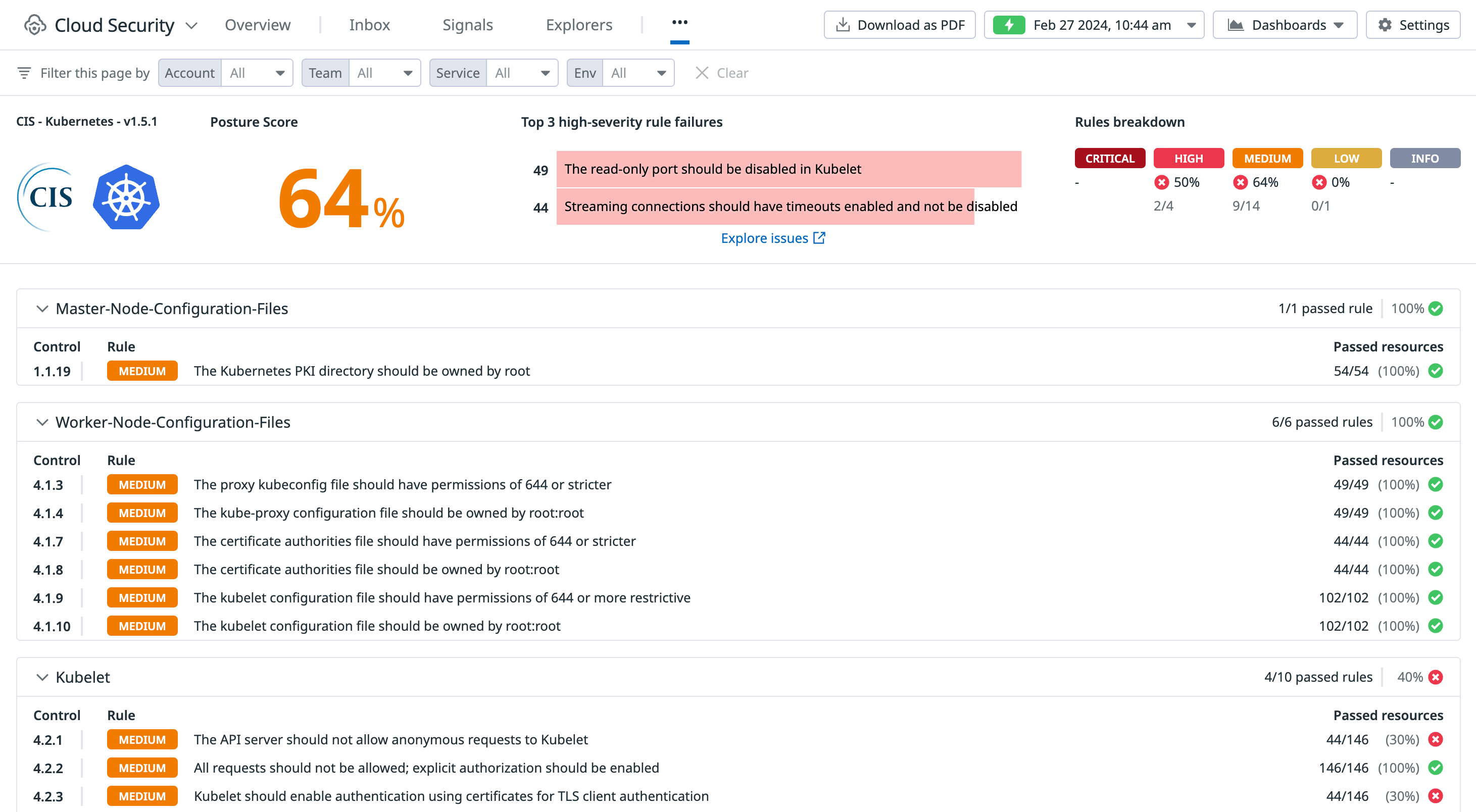
CSM provides a security posture score that helps you understand your security and compliance status using a single metric. The score represents the percentage of your environment that satisfies all of your active out-of-the-box cloud and infrastructure detection rules. You can obtain the score for your entire organization, or for specific teams, accounts, and environments, including Kubernetes deployments.
For an in-depth explanation on how the security posture score works, see Security posture score.
View security posture score for Kubernetes deployments
To view the security posture score for your Kubernetes deployments, navigate to the Security > Compliance page and locate the CIS Kubernetes frameworks reports.
View detailed reports for Kubernetes frameworks
To view a detailed report that gives you insight into how you score against the framework’s requirements and rules, click Framework Overview. On the framework page, you can download a copy of the report as a PDF or export it as a CSV.
Create your own Kubernetes detection rules
In addition to the out-of-the-box detection rules, you can also create your own Kubernetes detection rules by cloning an existing rule or creating a new one from scratch. Rules are written in the Rego policy language, a flexible Python-like language that serves as the industry standard for detection rules. For more information, see Writing Custom Rules with Rego.
After you create the detection rule, you can customize its severity (Critical, High, Medium, Low, or Info) and set alerts for real-time notifications to notify you when a new finding is detected.
Further reading
Additional helpful documentation, links, and articles: