- Essentials
- Getting Started
- Datadog
- Datadog Site
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Integrations
- Containers
- Dashboards
- Monitors
- Logs
- APM Tracing
- Profiler
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Synthetic Monitoring
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Integrations
- OpenTelemetry
- Developers
- Authorization
- DogStatsD
- Custom Checks
- Integrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Service Checks
- IDE Plugins
- Community
- Guides
- API
- Datadog Mobile App
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Sheets
- Monitors and Alerting
- Infrastructure
- Metrics
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Application Performance
- APM
- Continuous Profiler
- Database Monitoring
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- Real User Monitoring
- Product Analytics
- Synthetic Testing and Monitoring
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Quality Gates
- DORA Metrics
- Security
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Observability Pipelines
- Log Management
- Administration
Connect to Datadog over AWS PrivateLink
Datadog PrivateLink does not support the selected Datadog site.
This guide walks you through how to configure AWS PrivateLink for use with Datadog.
Overview
The overall process consists of configuring an internal endpoint in your VPC that local Datadog Agents can send data to. Your VPC endpoint is then peered with the endpoint within Datadog’s VPC.
Setup
Datadog exposes AWS PrivateLink endpoints in .
However, to route traffic to Datadog’s PrivateLink offering in from other regions, use inter-region Amazon VPC peering. Inter-region VPC peering enables you to establish connections between VPCs across different AWS regions. This allows VPC resources in different regions to communicate with each other using private IP addresses. For more details, see Amazon VPC peering.
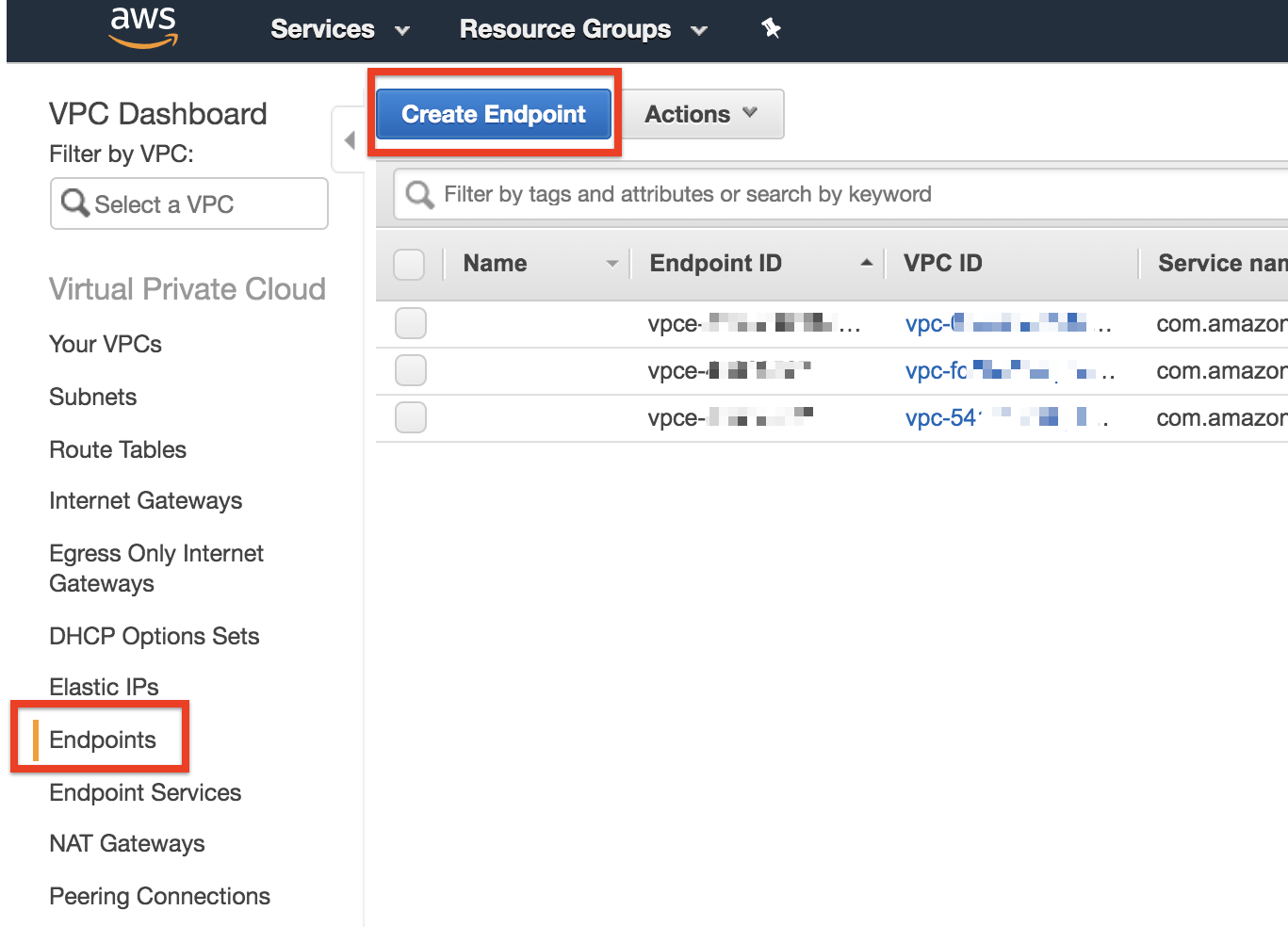
Connect the AWS Console to region and create a VPC endpoint.
Select Find service by name.
Fill the Service Name text box according to which service you want to establish AWS PrivateLink for:
| Datadog | PrivateLink service name | Private DNS name |
|---|---|---|
| Logs (Agent HTTP intake) | | |
| Logs (User HTTP intake) | | |
| API | | api. |
| Metrics | | metrics.agent. |
| Containers | | orchestrator. |
| Process | | process. |
| Profiling | | intake.profile. |
| Traces | | trace.agent. |
| Database Monitoring | | dbm-metrics-intake. |
| Remote Configuration | | config. |
Click Verify. If this does not return Service name found, reach out to Datadog support.
Choose the VPC and subnets that should be peered with the Datadog VPC service endpoint.
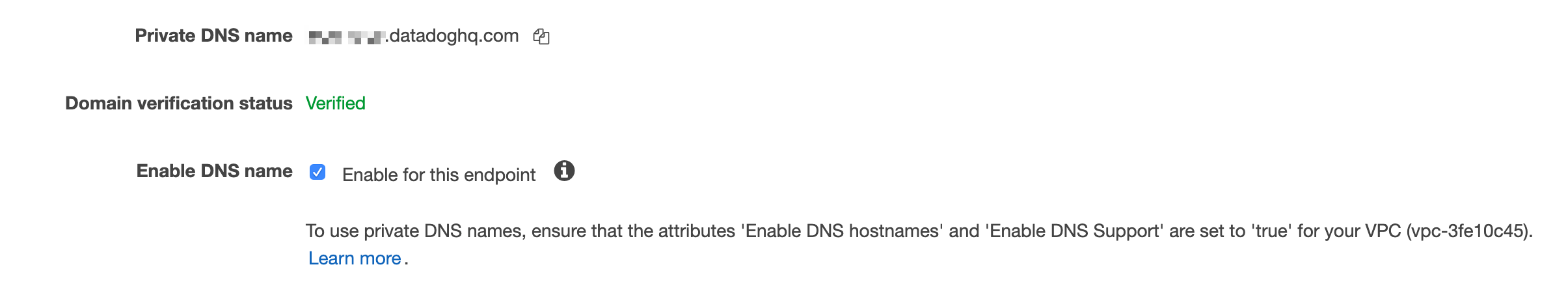
Make sure that for Enable DNS name, Enable for this endpoint is checked:
Choose the security group of your choice to control what can send traffic to this VPC endpoint.
Note: The security group must accept inbound traffic on TCP port
443.Click Create endpoint at the bottom of the screen. If successful, the following is displayed:
Click on the VPC endpoint ID to check its status.
Wait for the status to move from Pending to Available. This can take up to 10 minutes. Once it shows Available, you can use AWS PrivateLink.
If you are running a Datadog Agent version older than v6.19 or v7.19, to collect logs data, ensure your Agent is configured to send logs over HTTPS. If the data is not already there, add the following to the Agent
datadog.yamlconfiguration file:logs_config: force_use_http: trueIf you are using the container Agent, set the following environment variable instead:
DD_LOGS_CONFIG_FORCE_USE_HTTP=trueThis configuration is required when sending logs to Datadog with AWS PrivateLink and the Datadog Agent, and is not required for the Lambda Extension. For more details, see Agent log collection.
If your Lambda Extension loads the Datadog API Key from AWS Secrets Manager using the ARN specified by the environment variable
DD_API_KEY_SECRET_ARN, you need to create a VPC endpoint for Secrets Manager.Restart your Agent to send data to Datadog through AWS PrivateLink.
Amazon VPC peering
- Connect the AWS Console to region and create a VPC endpoint.
- Select Find service by name.
- Fill the Service Name text box according to the service you want to establish AWS PrivateLink for:
| Datadog | PrivateLink service name |
|---|---|
| Logs (Agent HTTP intake) | |
| Logs (User HTTP intake) | |
| API | |
| Metrics | |
| Containers | |
| Process | |
| Profiling | |
| Traces | |
| Database Monitoring | |
| Remote Configuration | |
Click Verify. If this does not return Service name found, reach out to Datadog support.
Next, choose the VPC and subnets that should be peered with the Datadog VPC service endpoint. Do not select Enable DNS name as VPC peering requires DNS to be manually configured.
Choose the security group of your choice to control what can send traffic to this VPC endpoint.
Note: The security group must accept inbound traffic on TCP port
443.Click Create endpoint at the bottom of the screen. If successful, the following is displayed:
- Click on the VPC endpoint ID to check its status.
- Wait for the status to move from Pending to Available. This can take up to 10 minutes.
- After creating the endpoint, use VPC peering to make the PrivateLink endpoint available in another region to send telemetry to Datadog over PrivateLink. For more information, read the Work With VPC Peering connections page in AWS.
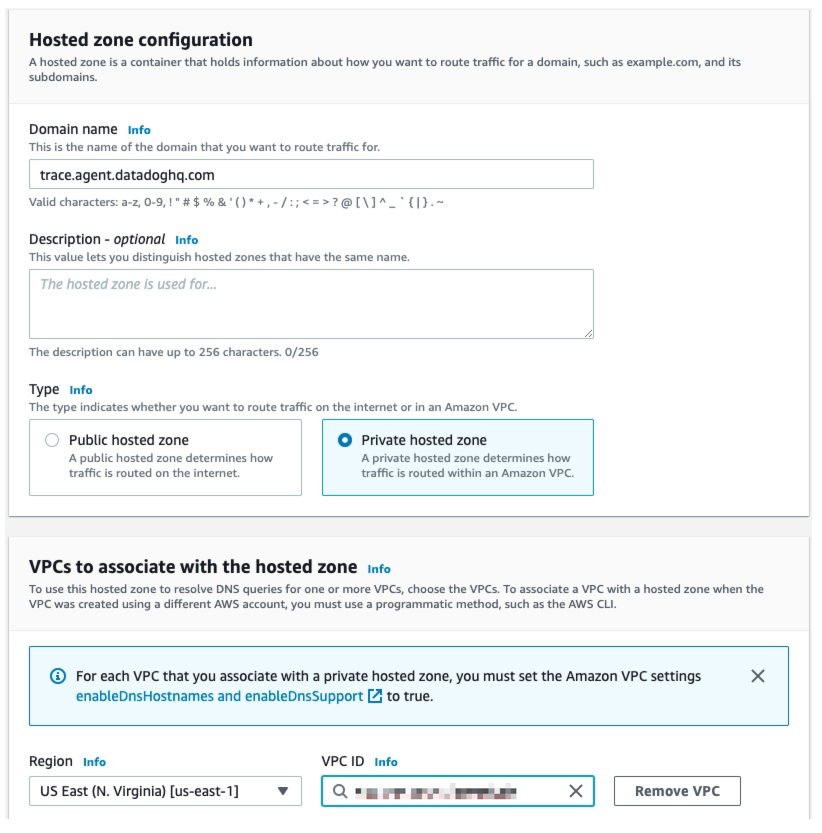
Amazon Route53
- Create a Route53 private hosted zone for each service you have created an AWS PrivateLink endpoint for. Attach the private hosted zone to the VPC in
.
Use the list below to map service and DNS name to different parts of Datadog:
| Datadog | PrivateLink service name | Private DNS name |
|---|---|---|
| Logs (Agent HTTP intake) | | agent-http-intake.logs. |
| Logs (User HTTP intake) | | http-intake.logs. |
| API | | api. |
| Metrics | | metrics.agent. |
| Containers | | orchestrator. |
| Process | | process. |
| Profiling | | intake.profile. |
| Traces | | trace.agent. |
| Database Monitoring | | dbm-metrics-intake. |
| Remote Configuration | | config. |
You can also find this information by interrogating the AWS API, DescribeVpcEndpointServices, or by using the following command:
aws ec2 describe-vpc-endpoint-services --service-names <service-name>`
For example, in the case of the Datadog metrics endpoint for :
aws ec2 describe-vpc-endpoint-services --service-names | jq '.ServiceDetails[0].PrivateDnsName'This returns metrics.agent., the private hosted zone name that you need in order to associate with the VPC which the Agent traffic originates in. Overriding this record grabs all Metrics-related intake hostnames.
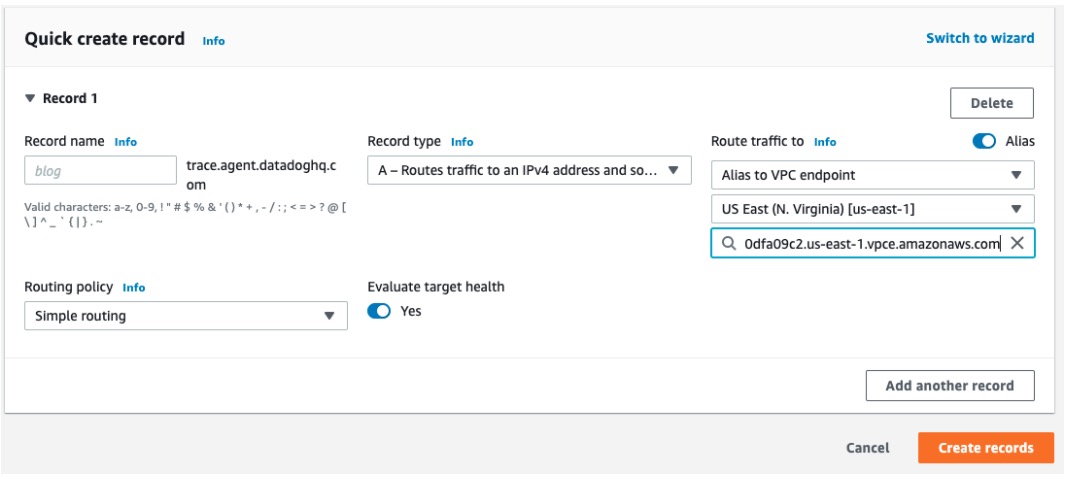
Within each new Route53 private hosted zone, create an A record with the same name. Toggle the Alias option, then under Route traffic to, choose Alias to VPC endpoint, , and enter the DNS name of the VPC endpoint associated with the DNS name.
Notes:
- To retrieve your DNS name, see the View endpoint service private DNS name configuration documentation.
- The Agent sends telemetry to versioned endpoints, for example,
[version]-app.agent.which resolves tometrics.agent.through a CNAME alias. Therefore, you only need to set up a private hosted zone formetrics.agent..
Configure VPC peering and routing between the VPC in
that contains the Datadog PrivateLink endpoints and the VPC in the region where the Datadog Agents run.If the VPCs are in different AWS accounts, the VPC containing the Datadog Agent must be authorized to associate with the Route53 private hosted zones before continuing. Create a VPC association authorization for each Route53 private hosted zone using the region and VPC ID of the VPC where the Datadog Agent runs. This option is not available in the AWS Console. It must be configured using the AWS CLI, SDK, or API.
Edit the Route53 hosted zone to add VPCs for other regions.
VPCs that have the Private Hosted Zone (PHZ) attached need to have certain settings toggled on, specifically
enableDnsHostnamesandenableDnsSupportin the VPCs that the PHZ is associated with. See Considerations when working with a private hosted zone.Restart the Agent to send data to Datadog through AWS PrivateLink.
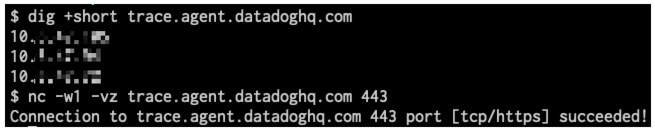
Troubleshooting DNS resolution and connectivity
The DNS names should resolve to IP addresses contained within the CIDR block of the VPC in , and connections to port 443 should succeed.
If DNS is resolving to public IP addresses, then the Route53 zone has not been associated with the VPC in the alternate region, or the A record does not exist.
If DNS resolves correctly, but connections to port 443 are failing, then VPC peering or routing may be misconfigured, or port 443 may not be allowed outbound to the CIDR block of the VPC in .
The VPCs with Private Hosted Zone (PHZ) attached need to have a couple of settings toggled on. Specifically, enableDnsHostnames and enableDnsSupport need to be turned on in the VPCs that the PHZ is associated with. See Amazon VPC settings.
Datadog Agent
If you are collecting logs data, ensure your Agent is configured to send logs over HTTPS. If the data is not already there, add the following to the Agent
datadog.yamlconfiguration file:logs_config: force_use_http: trueIf you are using the container Agent, set the following environment variable instead:
DD_LOGS_CONFIG_FORCE_USE_HTTP=trueThis configuration is required when sending logs to Datadog with AWS PrivateLink and the Datadog Agent, and is not required for the Lambda Extension. For more details, see Agent log collection.
If your Lambda Extension loads the Datadog API Key from AWS Secrets Manager using the ARN specified by the environment variable
DD_API_KEY_SECRET_ARN, you need to create a VPC endpoint for Secrets Manager.
Further reading
Additional helpful documentation, links, and articles: