- Principales informations
- Getting Started
- Datadog
- Site Datadog
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Intégrations
- Conteneurs
- Dashboards
- Monitors
- Logs
- Tracing
- Profileur
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Surveillance Synthetic
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Intégrations
- OpenTelemetry
- Développeurs
- Authorization
- DogStatsD
- Checks custom
- Intégrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Checks de service
- IDE Plugins
- Communauté
- Guides
- API
- Application mobile
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Alertes
- Infrastructure
- Métriques
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Universal Service Monitoring
- Conteneurs
- Sans serveur
- Surveillance réseau
- Cloud Cost
- Application Performance
- APM
- Profileur en continu
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Configuration de Postgres
- Configuration de MySQL
- Configuration de SQL Server
- Setting Up Oracle
- Setting Up MongoDB
- Connecting DBM and Traces
- Données collectées
- Exploring Database Hosts
- Explorer les métriques de requête
- Explorer des échantillons de requêtes
- Dépannage
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- RUM et Session Replay
- Product Analytics
- Surveillance Synthetic
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Visibility
- Exécuteur de tests intelligent
- Code Analysis
- Quality Gates
- DORA Metrics
- Securité
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Pipelines d'observabilité
- Log Management
- Administration
Configure SCIM with Azure Active Directory
Cette page n'est pas encore disponible en français, sa traduction est en cours.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
See the following instructions to synchronize your Datadog users with Azure Active Directory using SCIM.
For capabilities and limitations of this feature, see SCIM.
Prerequisites
SCIM in Datadog is an advanced feature available with the Infrastructure Pro and Infrastructure Enterprise plans.
This documentation assumes your organization manages user identities using an identity provider.
Datadog strongly recommends that you use a service account application key when configuring SCIM to avoid any disruption in access. For further details, see using a service account with SCIM.
When using SAML and SCIM together, Datadog strongly recommends disabling SAML just-in-time (JIT) provisioning to avoid discrepancies in access. Manage user provisioning through SCIM only.
Add Datadog to the Azure AD application gallery
- In your Azure portal, go to Azure Active Directory -> Enterprise Applications
- Click New Application -> Create your own application
- Type “Datadog” in the search box
- Select the Datadog application from the gallery
- Enter a name
- Click Create
Note: If you already have Datadog configured with Azure AD for SSO, go to Enterprise Applications and select your existing Datadog application.
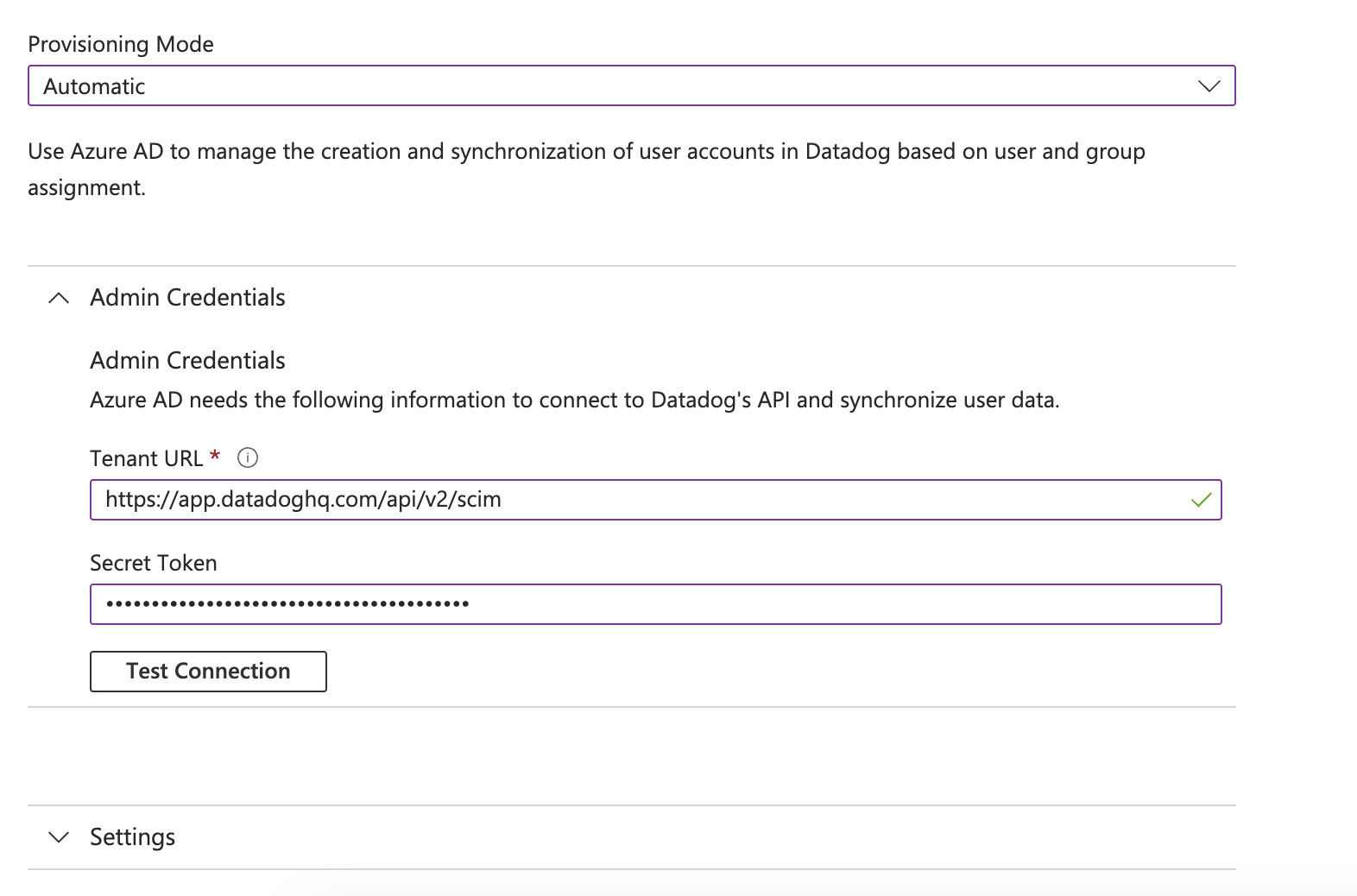
Configure automatic user provisioning
- In the application management screen, select Provisioning in the left panel
- In the Provisioning Mode menu, select Automatic
- Open Admin Credentials
- Complete the Admin Credentials section as follows:
- Tenant URL:
https:///api/v2/scimNote: Use the appropriate subdomain for your site. To find your URL, see Datadog sites. - Secret Token: Use a valid Datadog application key. You can create an application key on your organization settings page. To maintain continuous access to your data, use a service account application key.
- Tenant URL:
- Click Test Connection, and wait for the message confirming that the credentials are authorized to enable provisioning.
- Click Save. The mapping section appears. See the following section to configure mapping.
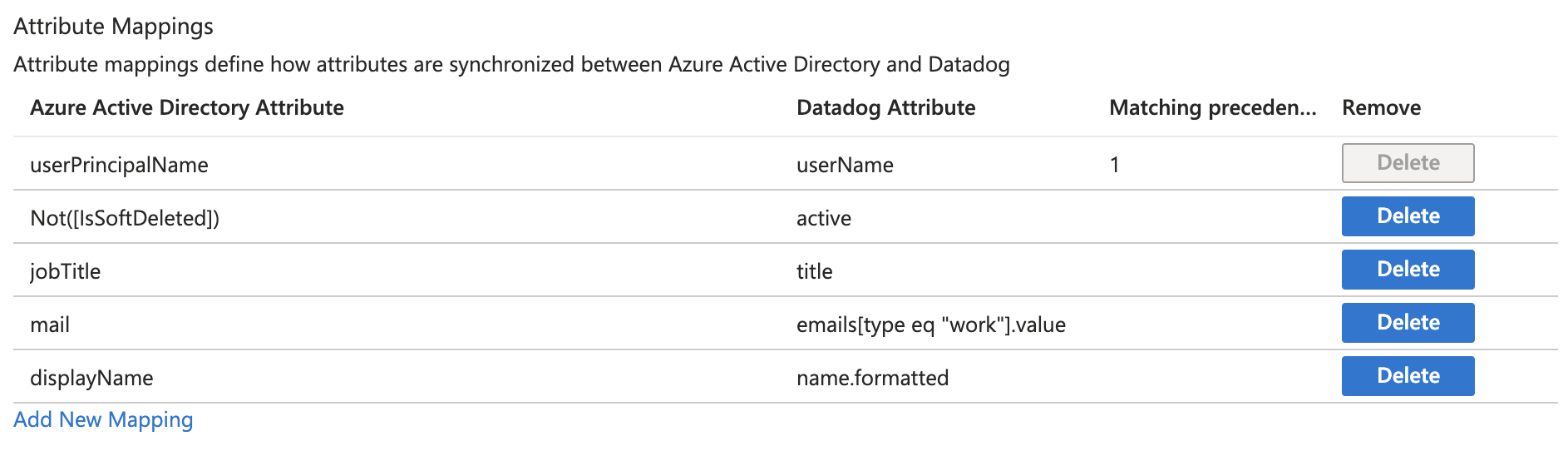
Attribute mapping
User attributes
Expand the Mappings section
Click Provision Azure Active Directory Users
Set Enabled to Yes
Click the Save icon
Under Target Object actions, ensure Create, Update, and Delete actions are selected
Review the user attributes that are synchronized from Azure AD to Datadog in the attribute mapping section. Set the following mappings:
Azure Active Directory Attribute Datadog Attribute userPrincipalNameuserNameNot([IsSoftDeleted])activejobTitletitlemailemails[type eq "work"].valuedisplayNamename.formattedAfter you set your mappings, click Save.
Group attributes
Group mapping is not supported.