- Principales informations
- Getting Started
- Datadog
- Site Datadog
- DevSecOps
- Serverless for AWS Lambda
- Agent
- Intégrations
- Conteneurs
- Dashboards
- Monitors
- Logs
- Tracing
- Profileur
- Tags
- API
- Service Catalog
- Session Replay
- Continuous Testing
- Surveillance Synthetic
- Incident Management
- Database Monitoring
- Cloud Security Management
- Cloud SIEM
- Application Security Management
- Workflow Automation
- CI Visibility
- Test Visibility
- Intelligent Test Runner
- Code Analysis
- Learning Center
- Support
- Glossary
- Standard Attributes
- Guides
- Agent
- Intégrations
- OpenTelemetry
- Développeurs
- Authorization
- DogStatsD
- Checks custom
- Intégrations
- Create an Agent-based Integration
- Create an API Integration
- Create a Log Pipeline
- Integration Assets Reference
- Build a Marketplace Offering
- Create a Tile
- Create an Integration Dashboard
- Create a Recommended Monitor
- Create a Cloud SIEM Detection Rule
- OAuth for Integrations
- Install Agent Integration Developer Tool
- Checks de service
- IDE Plugins
- Communauté
- Guides
- API
- Application mobile
- CoScreen
- Cloudcraft
- In The App
- Dashboards
- Notebooks
- DDSQL Editor
- Alertes
- Infrastructure
- Métriques
- Watchdog
- Bits AI
- Service Catalog
- API Catalog
- Error Tracking
- Service Management
- Infrastructure
- Universal Service Monitoring
- Conteneurs
- Sans serveur
- Surveillance réseau
- Cloud Cost
- Application Performance
- APM
- Profileur en continu
- Database Monitoring
- Agent Integration Overhead
- Setup Architectures
- Configuration de Postgres
- Configuration de MySQL
- Configuration de SQL Server
- Setting Up Oracle
- Setting Up MongoDB
- Connecting DBM and Traces
- Données collectées
- Exploring Database Hosts
- Explorer les métriques de requête
- Explorer des échantillons de requêtes
- Dépannage
- Guides
- Data Streams Monitoring
- Data Jobs Monitoring
- Digital Experience
- RUM et Session Replay
- Product Analytics
- Surveillance Synthetic
- Continuous Testing
- Software Delivery
- CI Visibility
- CD Visibility
- Test Visibility
- Exécuteur de tests intelligent
- Code Analysis
- Quality Gates
- DORA Metrics
- Securité
- Security Overview
- Cloud SIEM
- Cloud Security Management
- Application Security Management
- AI Observability
- Log Management
- Pipelines d'observabilité
- Log Management
- Administration
Create a Cloud SIEM Detection Rule
Cette page n'est pas encore disponible en français, sa traduction est en cours.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Si vous avez des questions ou des retours sur notre projet de traduction actuel, n'hésitez pas à nous contacter.
Overview
Datadog Cloud SIEM (Security Information and Event Management) unifies developer, operation, and security teams through one platform. Datadog provides a set of out-of-the-box detection rules for many features and integrations. View these rules in your SIEM Detection Rules list.
Create an out-of-the-box detection rule to help users find security insights through your Datadog integration. This guide provides steps for creating an Cloud SIEM detection rule and best practices to follow during the creation process.
To create a Datadog integration, see Create a New Integration.
Create a detection rule
Build a detection rule JSON schema
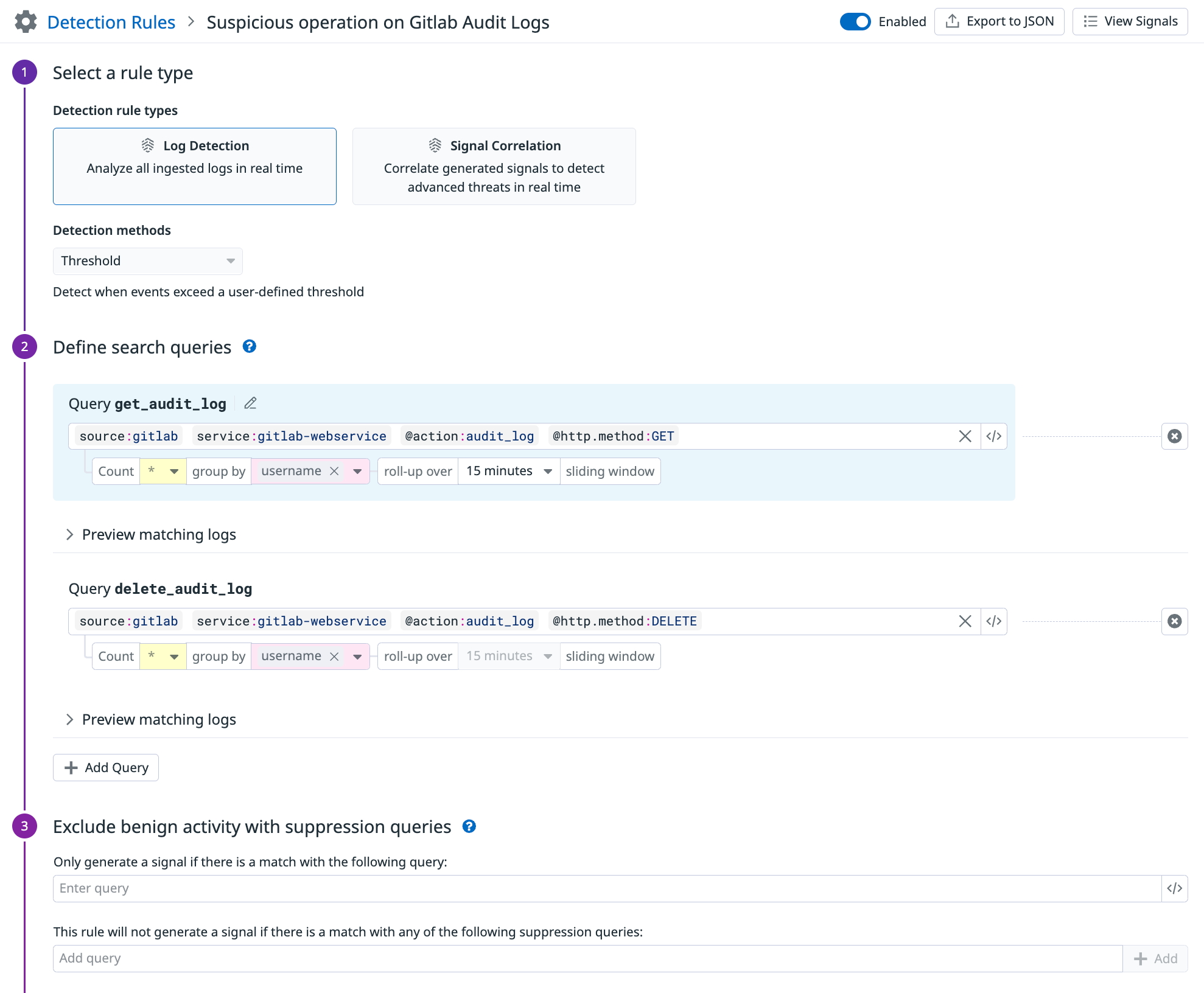
From Detection Rules, create a new rule.
Follow the best practices in this guide to configure your detection rule.
Click Export to JSON.
Save the JSON file and name it according to your detection rule title. For example,
your_integration_name_rule_name.json.In the detection rule JSON file, add and fill out the
partnerRuleId, and remove theisEnabledattribute. For more information, see Configuration best practices.
Open a pull request
Save the detection rule JSON file to your integration’s
assets/securityfolder.Open a pull request (PR) to update the corresponding integration folder in either the
integrations-extrasGitHub repository orMarketplaceGithub repository. The PR should include your detection rule JSON file, along with any new integration files.Datadog approves and merges the PR, and your integration-recommended monitor is pushed to production.
Verify your detection rule in production
To see the out-of-the-box detection rule, the relevant integration tile must be Installed in Datadog, and Cloud SIEM must be enabled.
- Find your detection rule in the Detection Rules list, and expand it.
- Ensure that its logos render correctly.
- Verify that the rule is enabled.
Configuration best practices
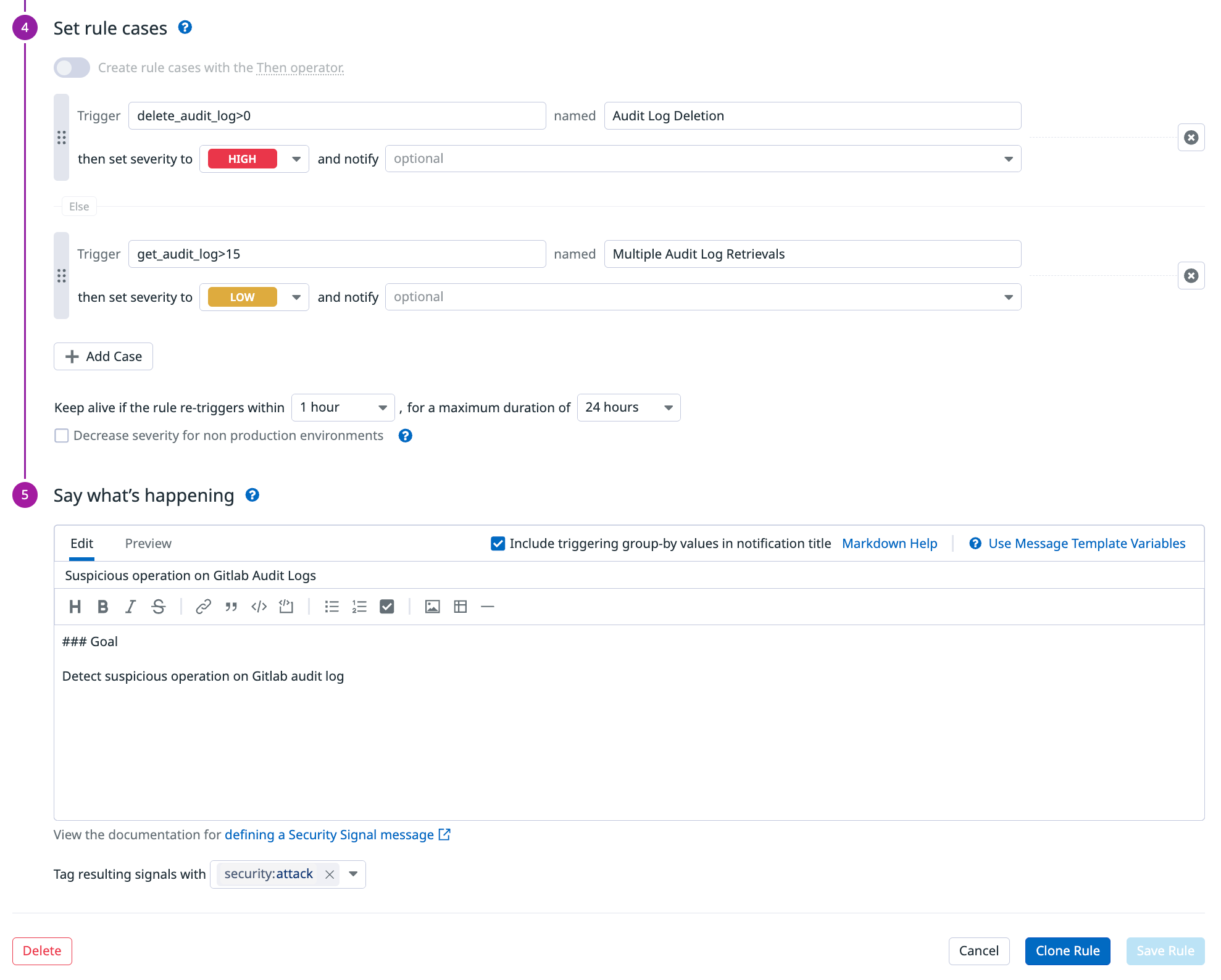
In addition to the detection rule definition, the partnerRuleId field is required for partner contributed detection rules. The isEnabled field should be removed as it does not apply to partner contributed detection rules.
| Description | Examples | |
|---|---|---|
| partnerRuleId | Unique identifier for the rule, following the format ext-00*-*** where * could be any alphanumeric characters. | ext-003-bzd |
Example of a well-defined detection rule
Selecting a rule type and defining search queries:
Setting rule cases and writing the notification message:
For more information, see the documentation on configuring a detection rule.
Understanding validation messages
Rule JSON parsing
File=<FILE_PATH> in collection=<COLLECTION> is an invalid JSON: error=<ERROR>
This error means that the JSON located at <FILE_PATH> is considered invalid JSON
Rule ID/Rule name
partnerRuleId is empty for rule name="<RULE_NAME>" - partnerRuleId=<NEW_RULE_ID> is available
A partnerRuleId is required for each rule and is missing. Use the generated <NEW_RULE_ID>.
partnerRuleId=<RULE_ID> is in the incorrect format for rule name="<RULE_NAME>", it must follow the format=^[a-z0-9]{3}-[a-z0-9]{3}-[a-z0-9]{3}$ - partnerRuleId=<NEW_RULE_ID> is available
The rule name is not in the correct format. Use the generated partnerRuleId: <NEW_RULE_ID> to fix the issue.
Duplicate partnerRuleId=<RULE_ID> for rule name="<RULE_NAME>" - <RULE_ID_KEY> must be unique and it is already used in rule_ids="<RULE_IDS>" - <RULE_ID_KEY>=<NEW_RULE_ID> is available
Each partnerRuleId must be unique. The current ID is already being used. The newly generated partnerRuleId is available.
Duplicate name="<RULE_NAME>" for <RULE_ID_KEY>=<RULE_ID> - name must be unique.
Each rule name must be unique. The current name is already being used. Update the rule name to be unique.
MITRE tags
The rule with partnerRuleId=<RULE_ID> contains a MITRE tag tactic but it does not contain the tag `security:attack`, please add it
When a rule contains a MITRE tag tactic:<TAG_VALUE>, the tag security:attack must be added to the list of tags.
The MITRE tactic/technique tag=<TAG> for partnerRuleId=<RULE_ID> appears to be incorrect (i.e. it does not exist in the MITRE framework).
The listed tactic/technique tag <TAG> does not follow the MITRE framework. Please select a valid MITRE tag.
Cases
The case status <CASE_STATUS> for <RULE_ID_KEY>=<RULE_ID> is incorrect, it should be one of <STATUS_LIST>.
The case status must be either CRITICAL, HIGH, MEDIUM, LOW, or INFO.
The case ordering for partnerRuleId=<RULE_ID> is incorrect, please modify to order cases from the highest severity to the lowest.
Each rule definition must be ordered by decreasing severity. Please reorder the cases into CRITICAL, HIGH, MEDIUM, LOW, and INFO.
Source tags
source=<SOURCE> in the tags of the rule with partnerRule=<RULE_ID> is not supported by Datadog documentation.
Reach out to Datadog to address the issue.
Rule content validation/ rule update
<RULE_ID_KEY>=<RULE_ID> name="<RULE_NAME>" - error=<ERROR>
Reach out to Datadog to address the issue.
Internal failure for <RULE_ID_KEY>=<RULE_ID> name="<RULE_NAME>"- Contact Datadog Team
Reach out to Datadog to address the issue.
Further reading
Documentation, liens et articles supplémentaires utiles: